SOC Sim: Apr 30
Worked through a 4-alert SOC simulation queue covering phishing email triage and firewall events. Used Splunk for log investigation and VirusTotal and Cisco Talos for threat intel. Classified two active phishing campaigns — one blocked at the perimeter, one requiring immediate escalation for potential credential compromise.
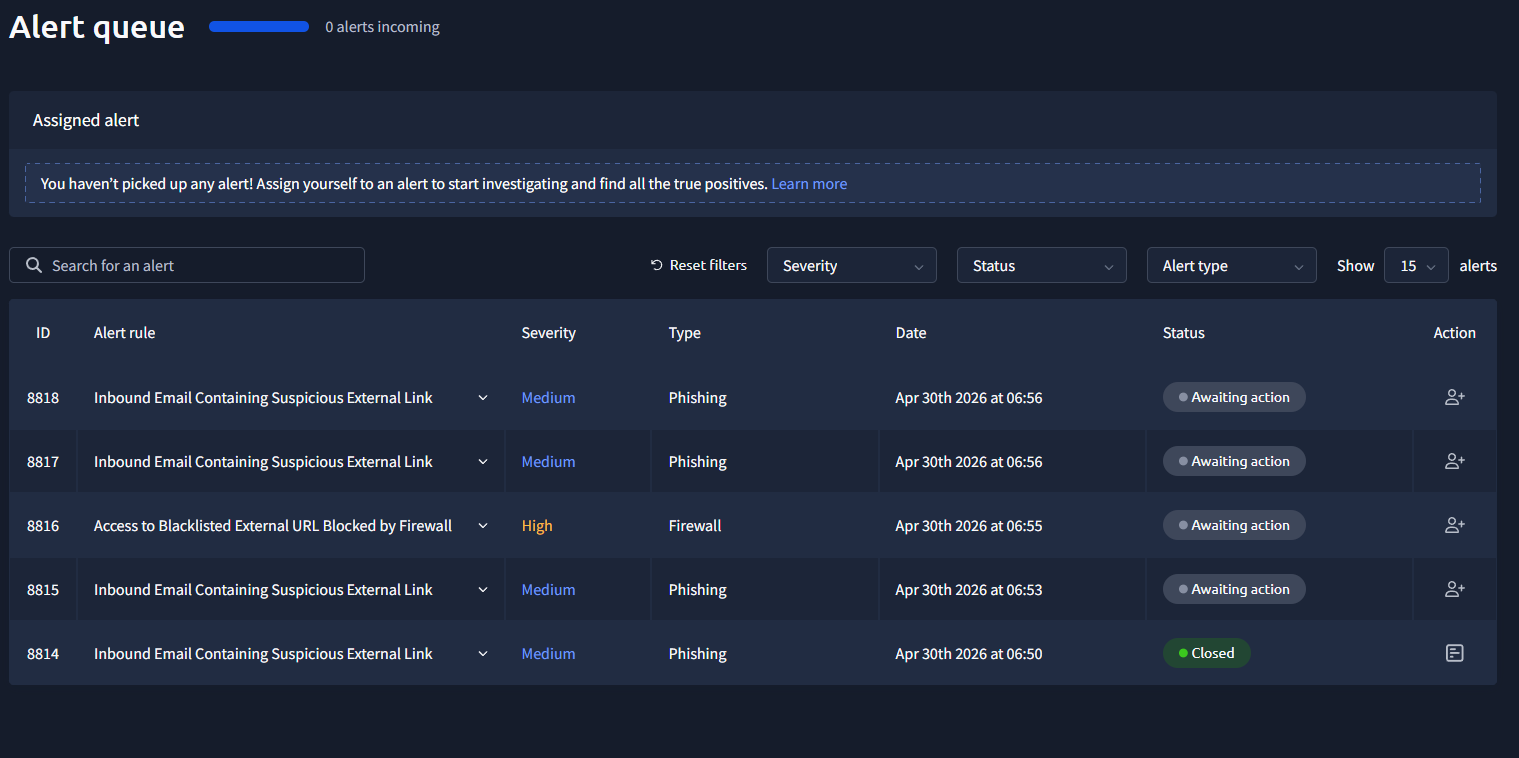
Alert Queue
starting with alert 8814 first, then we check the full queue and prioritize from there.
Alert 8814 — Inbound Suspicious Email
we got an alert. it was triggered by an inbound email containing one or more external links with potentially suspicious characteristics. the alert description says to check firewall or proxy logs to see if any endpoints accessed the URLs and whether those connections were allowed or blocked.
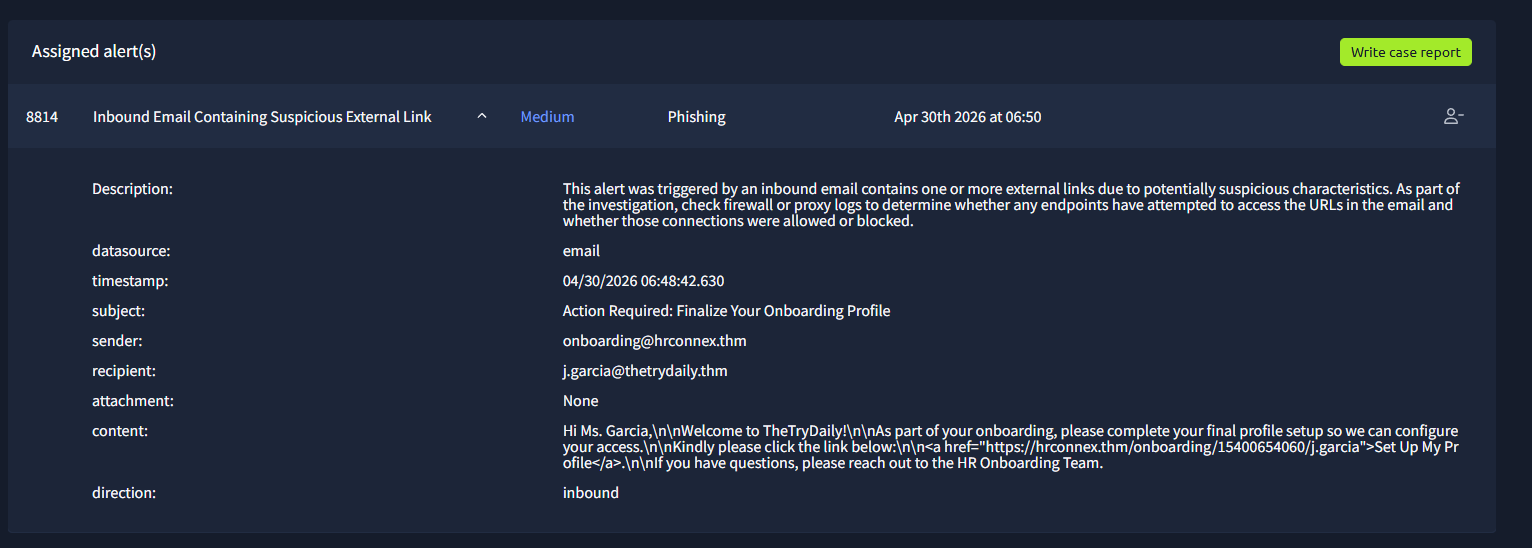
we look that up in Splunk and get the full event.
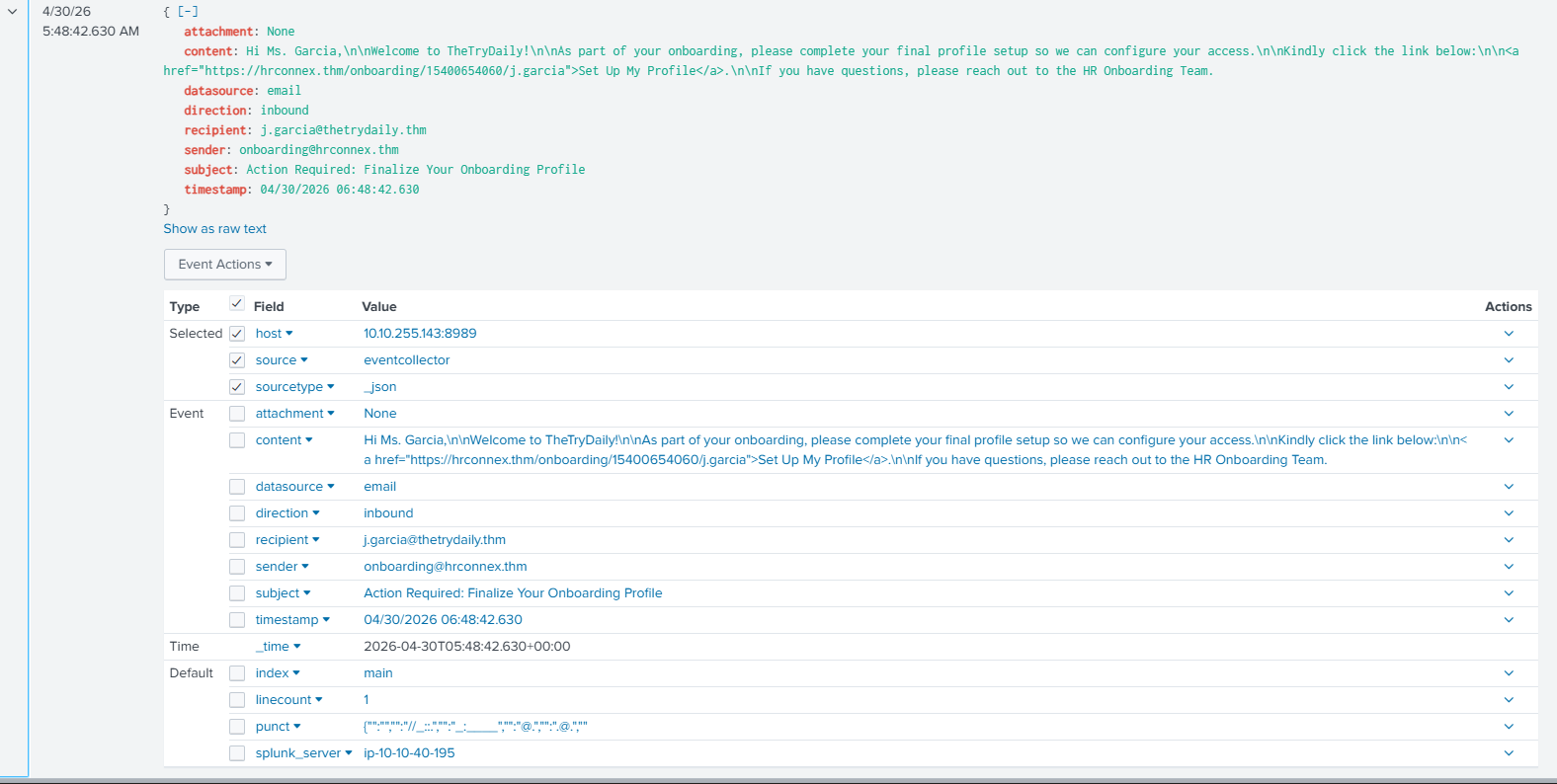
let's see if there was any connection made to hrconnex[.]thm.
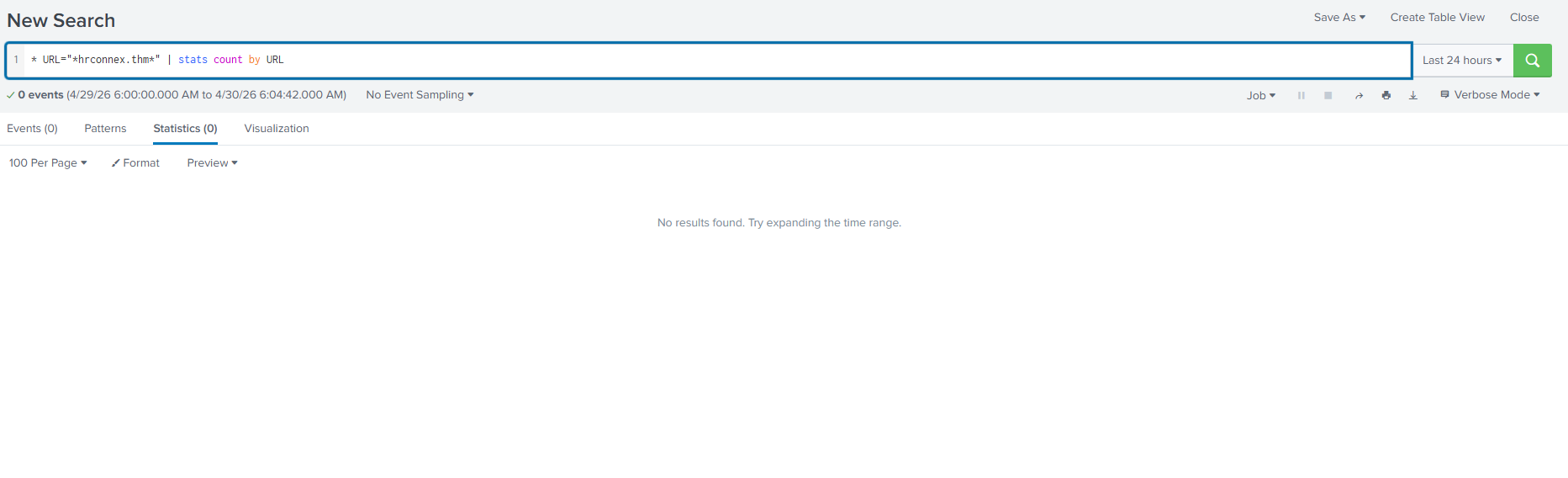
we didn't see any connection made to hrconnex[.]thm. we can classify this as a false positive and write the incident report.
| Time of Activity | 04/30/2026 06:48:42.630 |
| List of Related Entities | Sender: onboarding@hrconnex[.]thm Receiver: j.garcia@thetrydaily[.]thm URL: hxxps://hrconnex[.]thm/onboarding/15400654060/j.garcia |
| Reason for Classifying as False Positive | The alert triggered on an email from onboarding@hrconnex[.]thm to j.garcia@thetrydaily[.]thm containing a suspicious URL. No outbound HTTP requests to hrconnex[.]thm were observed from j.garcia's host during the timeframe. The email was received but the link was not clicked, confirming no user interaction with the URL occurred. |
Alert 8816 — Blacklisted URL Blocked
back to the queue. let's prioritize the high severity alert.
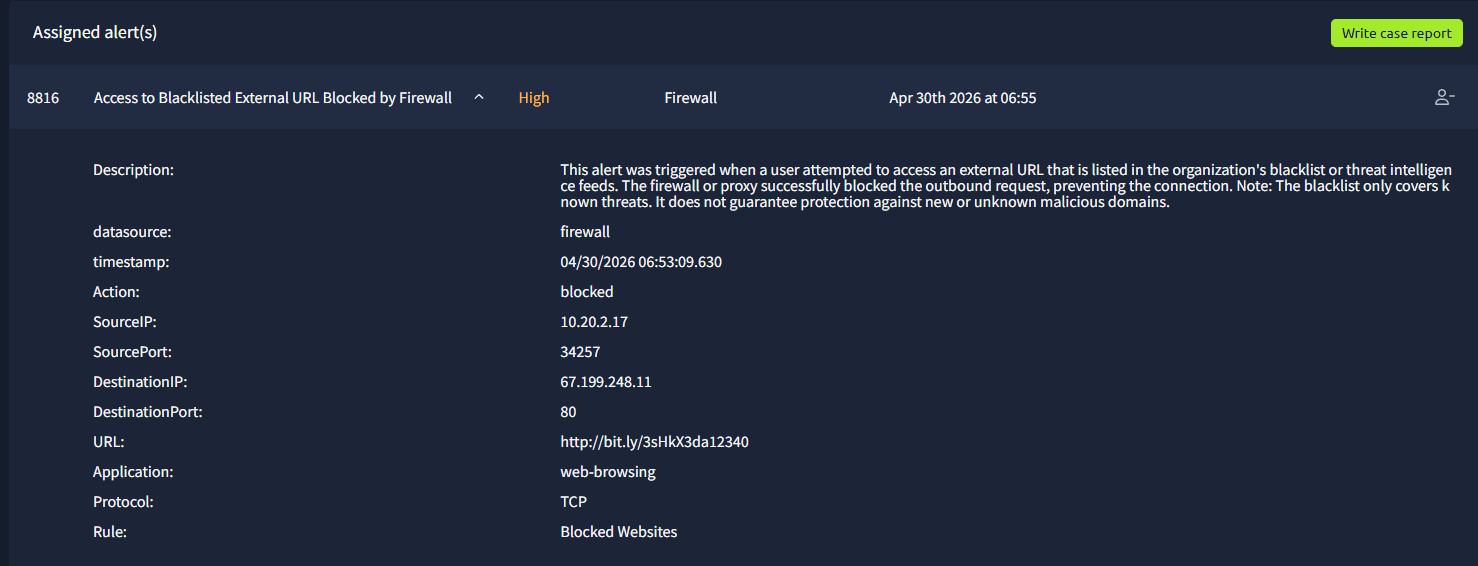
this alert fired when a user attempted to access an external URL on the org's threat intelligence blacklist. the firewall blocked the request. the alert note says the blacklist only covers known threats and does not guarantee protection against new or unknown malicious domains.
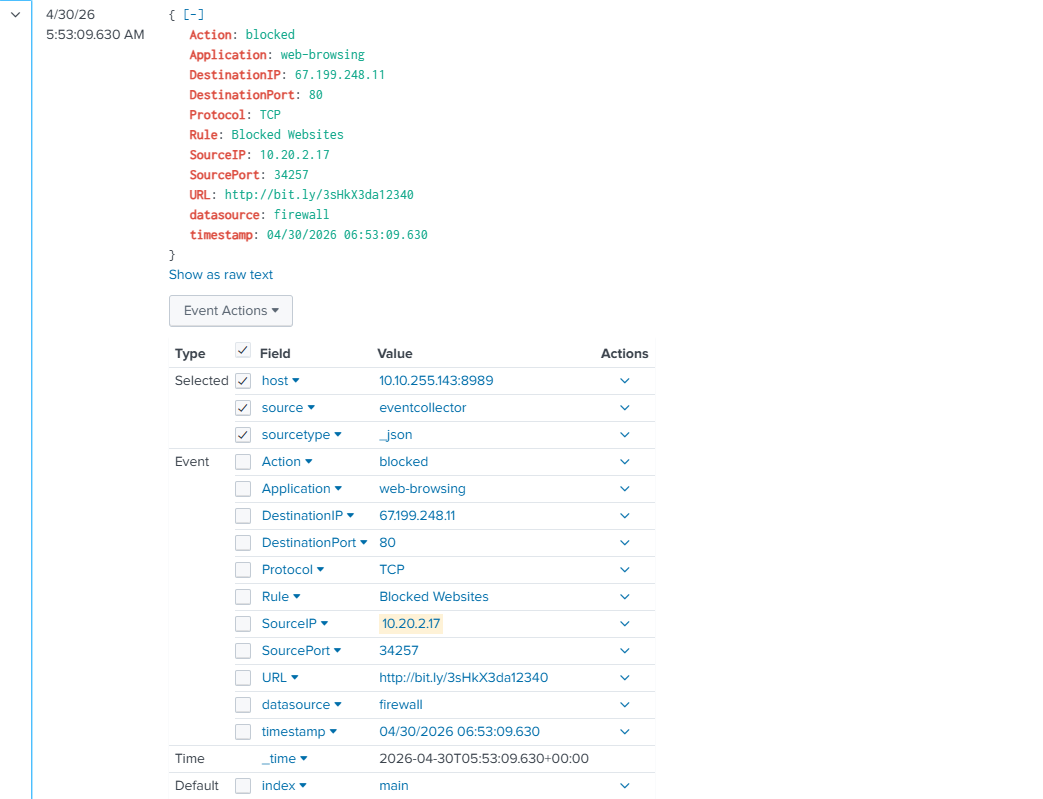
so we know this is blocked. let's see what other sites the user tried to access.
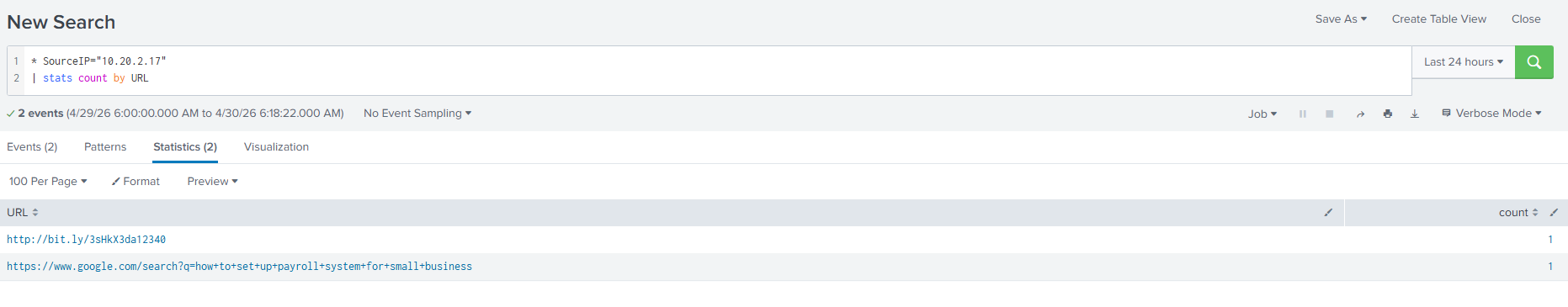
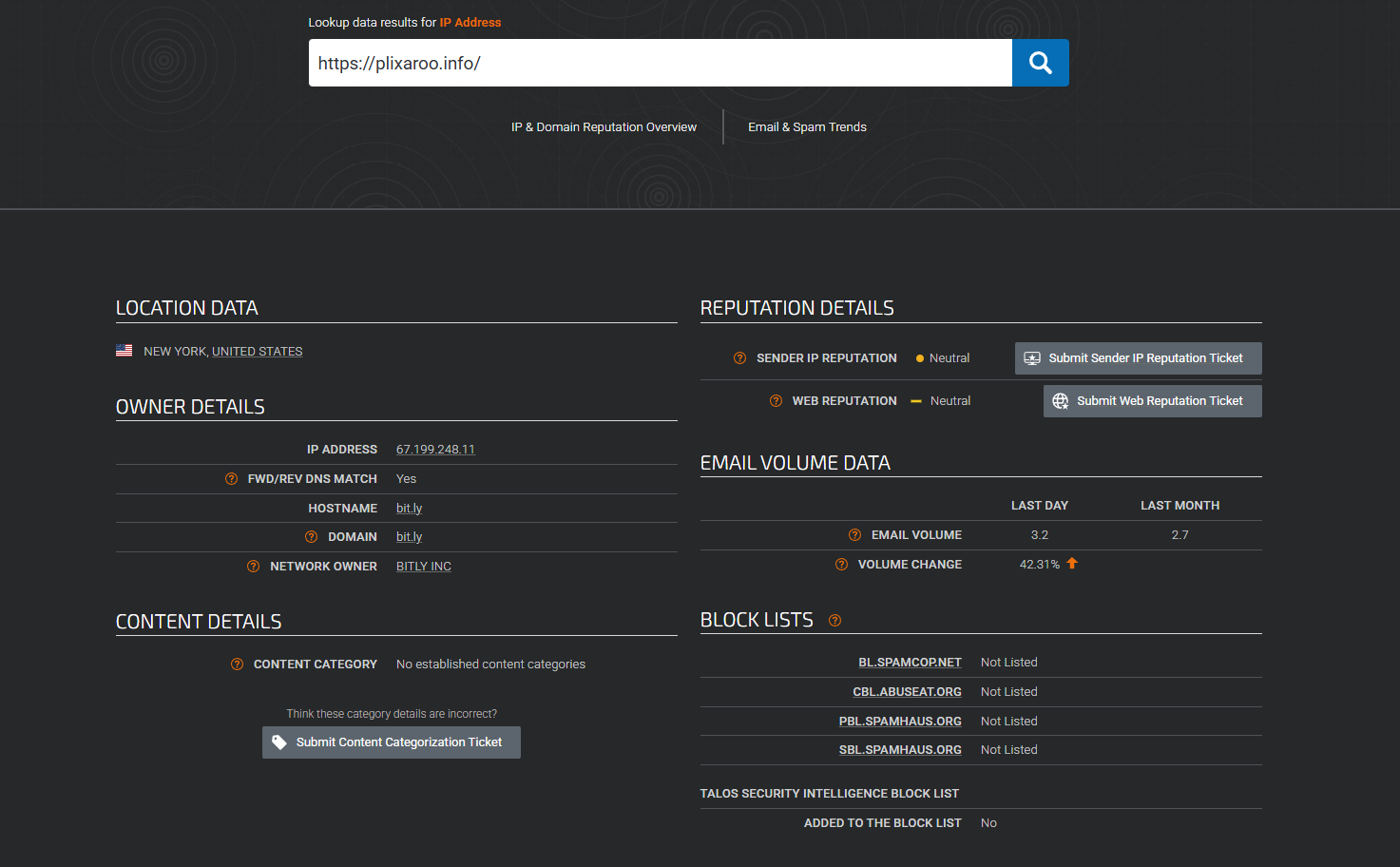
checking the reputation of the site we see it's newly registered and tagged as suspicious.
however looking at Cisco Talos we don't see anything sus.
let's close this as true positive and move on.
| List of Affected Entities | Hannah Harris, HR — 10[.]20[.]2[.]17 |
| Reason for Classifying as True Positive | Hannah Harris tried accessing a shortened URL hxxp://bit[.]ly/3sHkX3da12340 that redirected to hxxps://plixaroo[.]info/. Both URLs had hits on VirusTotal classifying it as suspicious and phishing. The attempt was blocked by the firewall. |
| Reason for Escalating the Alert | No need for escalation. |
| Recommended Remediation Actions | Block outbound connections to hxxps://plixaroo[.]info/ and 67[.]199[.]248[.]11 as this was a link associated to a phishing attempt from urgents@amazon[.]biz. |
| Attack Indicators | Value |
|---|---|
| Phishing email | urgents@amazon[.]biz |
| Phishing link | hxxp://bit[.]ly/3sHkX3da12340 |
| Redirect | hxxps://plixaroo[.]info/ |
| Destination IP | 67[.]199[.]248[.]11 |
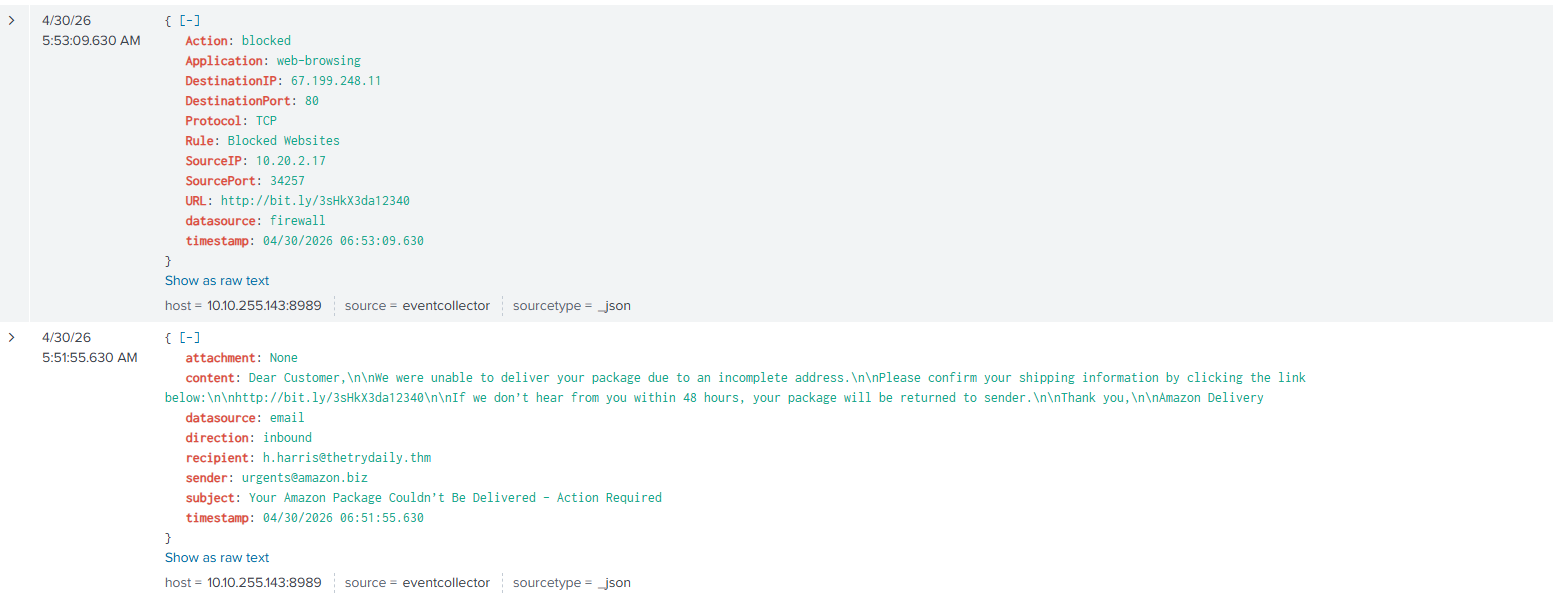
Alert 8815 — Amazon Phishing Email
this alert was also triggered by an inbound email with suspicious external links. it happened at 04/30/2026 06:51:55.630. let's investigate — this one is connected to the alert we just closed.
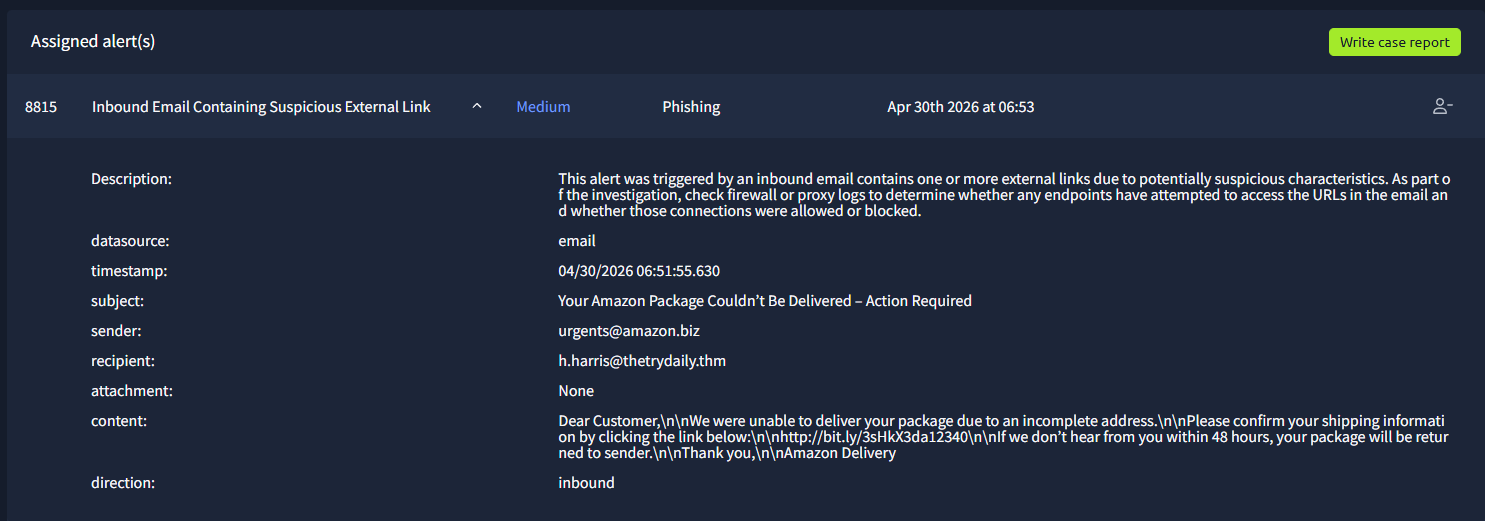
searching Splunk for h.harris gives us both events together. we now have the full view of the attack: a phishing email from urgents@amazon[.]biz sent to h.harris@thetrydaily[.]thm, which Harris eventually accessed, but the connection was blocked by the firewall.
let's close this report and update the previous one as well.
| Time of Activity | 04/30/2026 06:51:55.630 |
| List of Affected Entities | Hannah Harris, HR — 10[.]20[.]2[.]17 — h.harris@thetrydaily[.]thm |
| Reason for Classifying as True Positive | Hannah Harris received a phishing email from urgents@amazon[.]biz. The link sent was not associated with Amazon in any way and redirects to hxxps://plixaroo[.]info/, a domain flagged as malicious on VirusTotal. Harris clicked the link but the connection was blocked by the firewall. |
| Reason for Escalating the Alert | No reason for escalating this alert as the connection was blocked by the firewall. |
| Recommended Remediation Actions | Block emails from urgents@amazon[.]biz and outbound connections to hxxps://plixaroo[.]info/. Notify Hannah Harris about the phishing attempt and advise caution with similar emails. |
| Attack Indicators | Value |
|---|---|
| Phishing email | urgents@amazon[.]biz |
| Phishing link | hxxp://bit[.]ly/3sHkX3da12340 |
| Redirect | hxxps://plixaroo[.]info/ |
| Destination IP | 67[.]199[.]248[.]11 |
Alert 8817 — Microsoft Impersonation (Escalated)
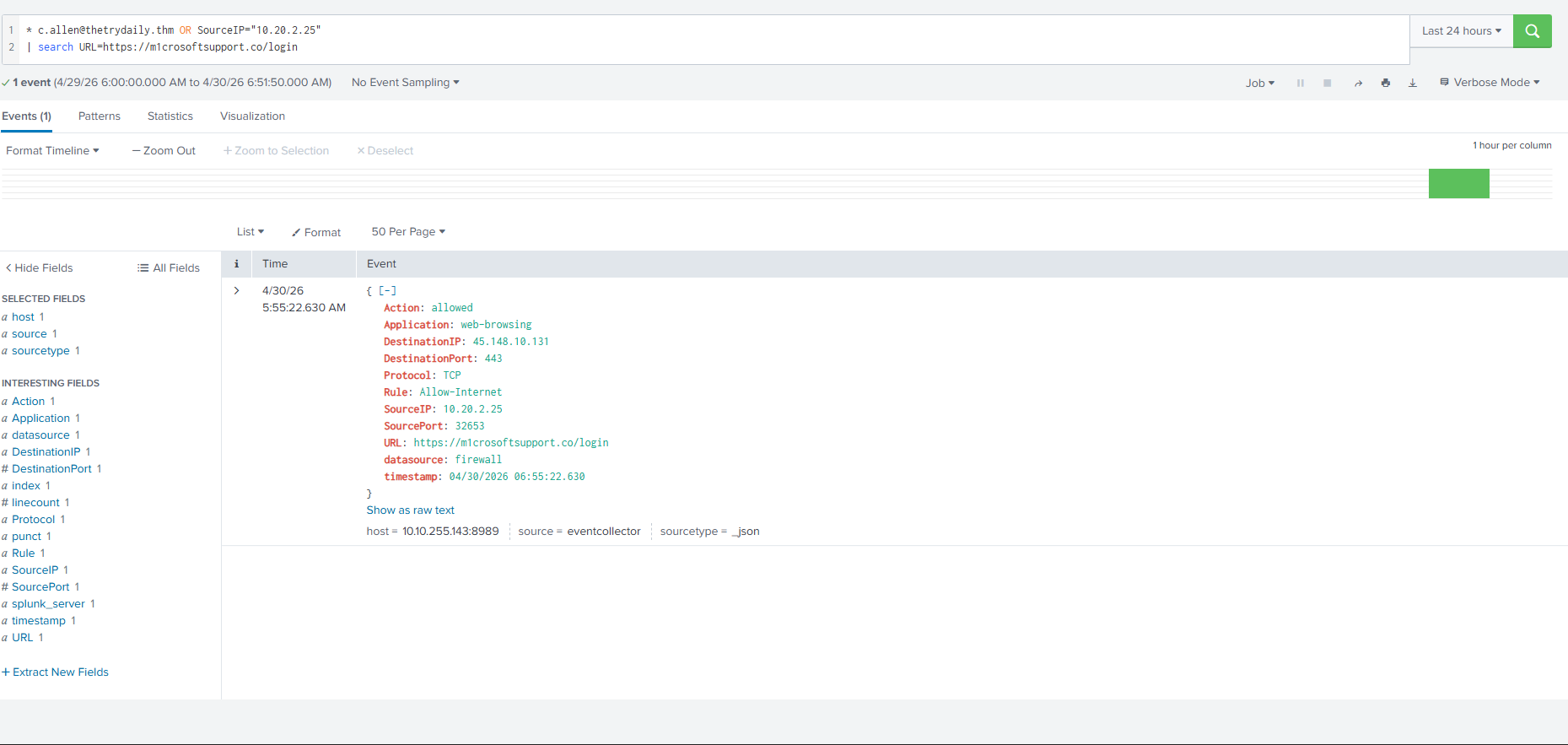
this is a clear phishing attempt. the sender is using typosquatting — m1crosoftsupport, not microsoft. let's review the logs for any access to the link.
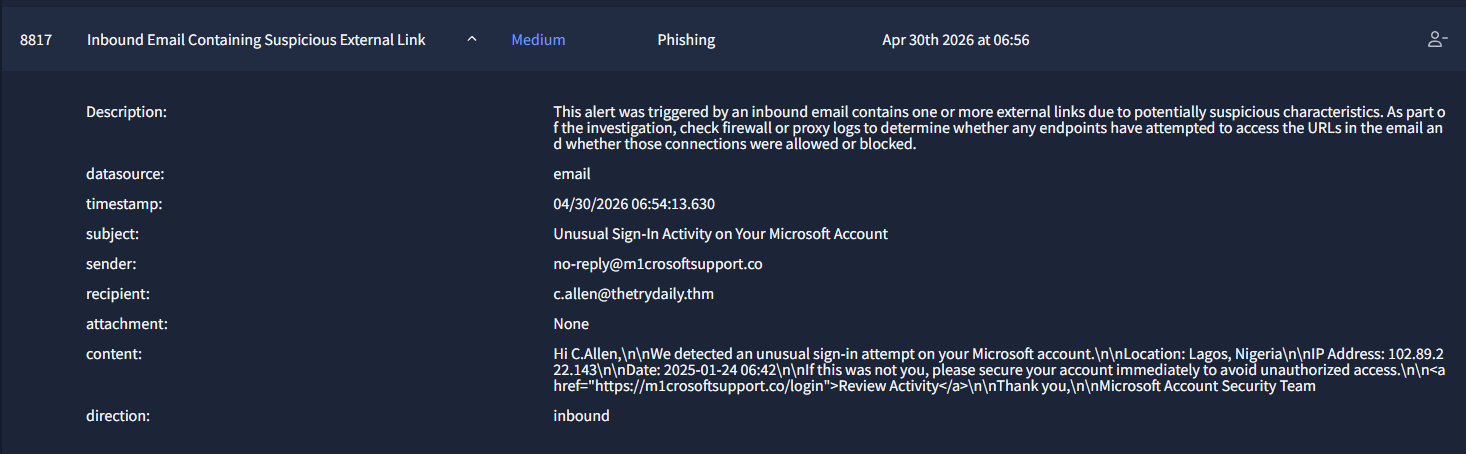
this is bad. the firewall has allowed an outbound connection. let's escalate this immediately.
| Time of Activity | 04/30/2026 06:54:13.630 |
| List of Affected Entities | c.allen@thetrydaily[.]thm — 10[.]20[.]2[.]25 |
| Reason for Classifying as True Positive | c.allen received a phishing email from no-reply@m1crosoftsupport[.]co disguising as Microsoft support. Upon further review, allen accessed the link hxxps://m1crosoftsupport[.]co/login at 04/30/2026 06:55:22. |
| Reason for Escalating the Alert | The outbound connection from the phishing email was allowed. Immediate isolation is needed. |
| Recommended Remediation Actions | Isolate the host associated to c.allen. Investigate c.allen's host (10[.]20[.]2[.]25) for credential harvesting, session tokens, or any follow-on malware dropped after the connection to m1crosoftsupport[.]co/login. Check browser history, running processes, and network connections. Force password reset for c.allen. |
| Attack Indicators | Value |
|---|---|
| Phishing email | no-reply@m1crosoftsupport[.]co |
| Phishing link | hxxps://m1crosoftsupport[.]co/login |
| Destination IP | 45[.]148[.]10[.]131 |
- →not all true positives are the same. a blocked attempt is contained. an allowed connection to a credential harvesting page is an active incident that needs escalation
- →URL shorteners hide the real destination. always resolve them and check the actual domain, not just the shortlink
- →low VT detection ratios do not mean clean. plixaroo[.]info had 1/92 detections. newly registered phishing infrastructure often shows minimal detections early
- →typosquatting gets past users who are not paying close attention. m1crosoftsupport[.]co is close enough to fool someone who quickly reads the sender field
- →correlating related alerts tells a richer story. alerts 8815 and 8816 were the same attack chain. investigating them together revealed the full timeline: email received, link clicked, connection blocked
two separate phishing campaigns running at the same time against the same org. one got blocked, one went through. that gap between a contained alert and an active credential compromise is where SOC work actually matters. this sim was good for building the habit of looking across related alerts rather than just closing them one by one.