ItsyBitsy
Investigated a potential C2 communication alert in Elastic/Kibana using a week's worth of HTTP connection logs. Identified Bitsadmin as the LOtL binary used to reach out to Pastebin, retrieved the malicious URI, and recovered the staged secret file.
Scoping the Investigation
we got the answer by filtering the date Absolute from Mar 1, 2022 @ 00:00:00.000 to Mar 31, 2022 @ 23:59:59.999
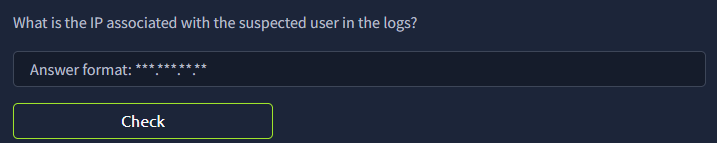
the user Browne is the one suspected of having a potential C2 communication. to get his IP address, we just have to add the IP address field.
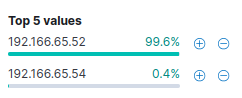
there's only 2 IP associated with Browne. the IP address 192.166.65.54 has only 2 logged entries, upon inspection it's using a different user_agent called bitsadmin. upon further research, this is a legitimate tool used by Administrator and often abused by attackers.
C2 Tool, Destination, and File
we already know this from the previous question since it was using Bitsadmin
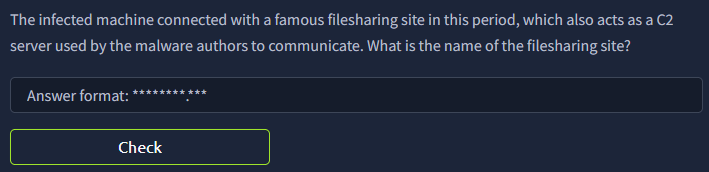
checking at the host, it connected to Pastebin.com with a random string assigned for the uri.
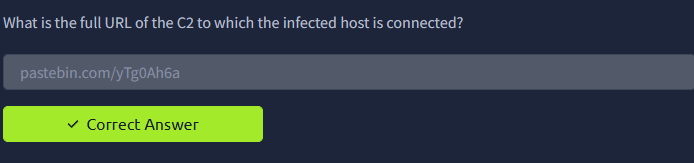
connecting the random uri string yTg0Ah6a
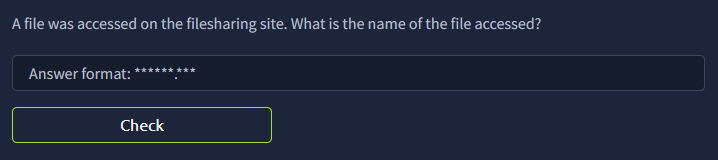
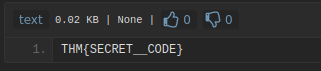
going to the site, there is a text file called Secret.txt
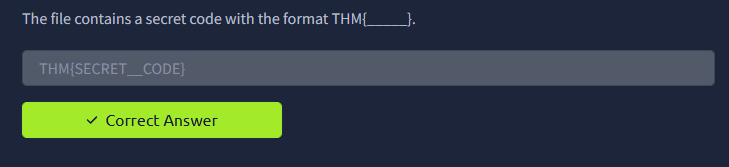
it contains a secret code
- →Bitsadmin running in a user context is an immediate red flag. that's not what it's there for
- →Pastebin works as a dead drop because it's not suspicious enough to get blocked by default. easy to stage something there and pull it down later
- →set the absolute time filter in Kibana first, before anything else. the logs don't mean much without it
- →the columns you add to your Kibana view actually matter. adding IP and user_agent cut down my read time a lot