Invite Only
Threat intelligence analysis on two flagged indicators (IP and SHA256 hash). Traced execution parents, dropped files, and malware family using VirusTotal. Identified AsyncRAT as the malware family, ClickFix as the phishing technique, and Discord invite hijacking as the delivery mechanism.
Hash and File Analysis
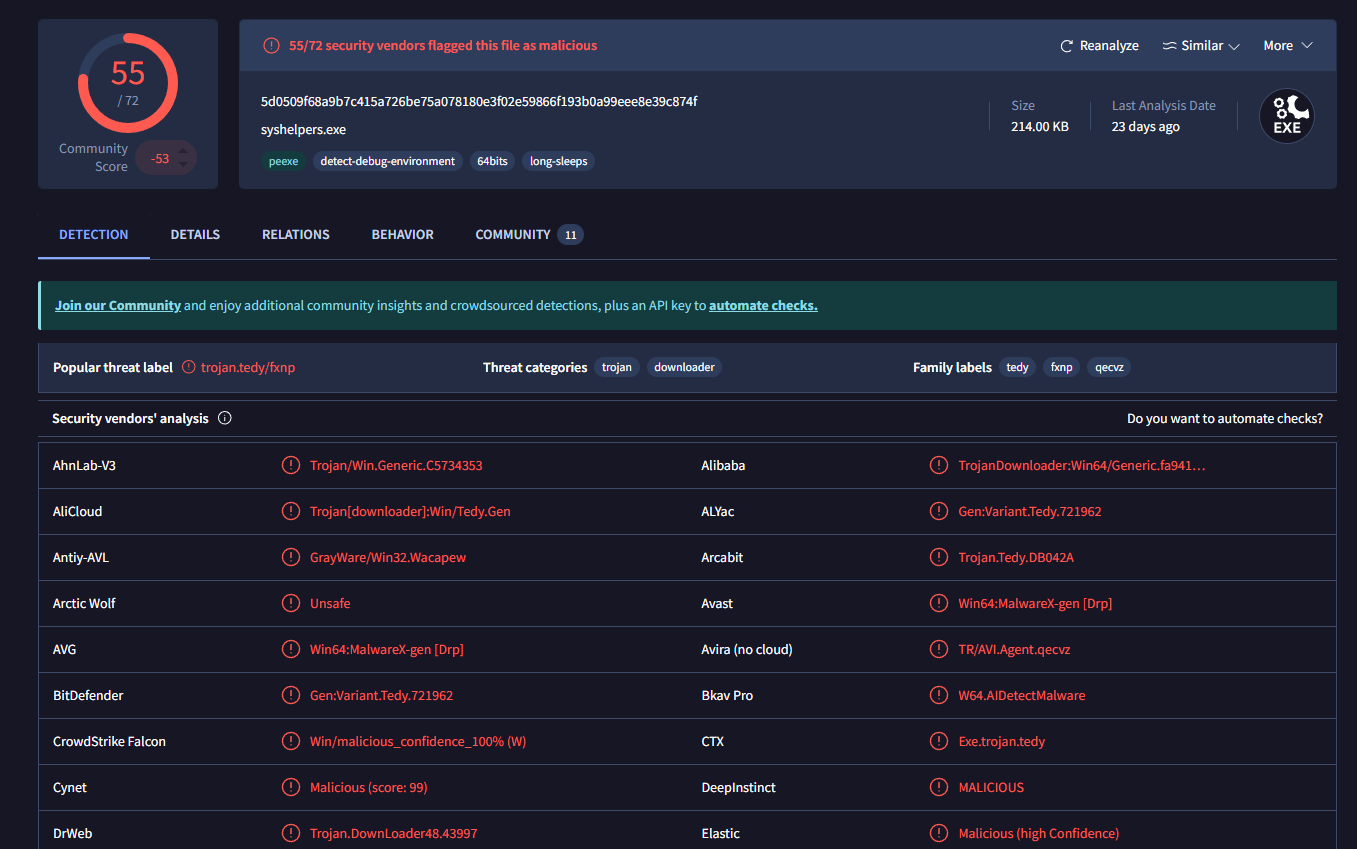
using VirusTotal, I identified the file flagged by the L1 analyst.
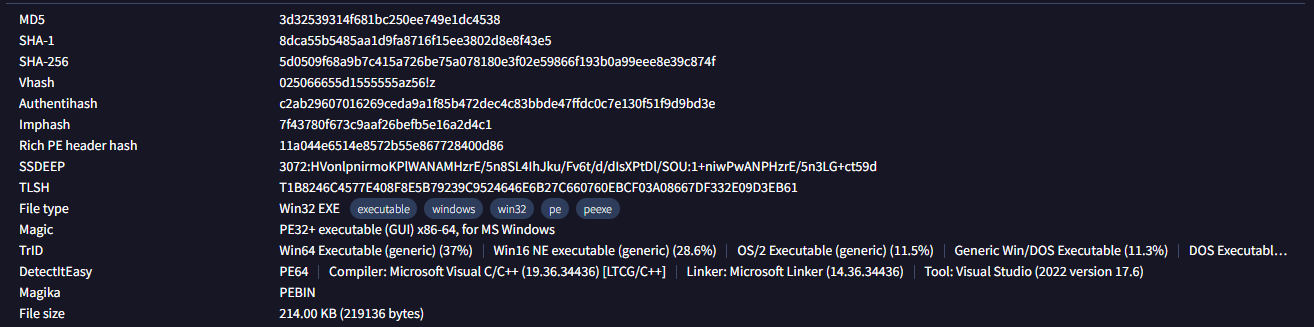
looking further to the VirusTotal report, we can see the associated file type
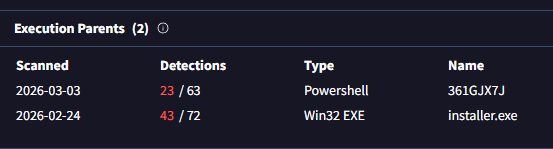
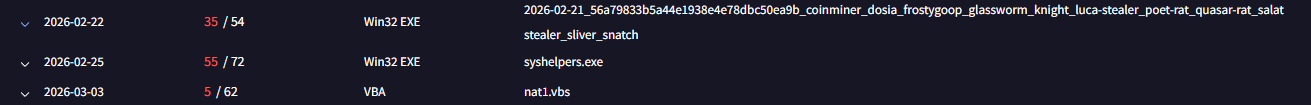
moving to the Relations tab we can see the execution parents and their respective hashes
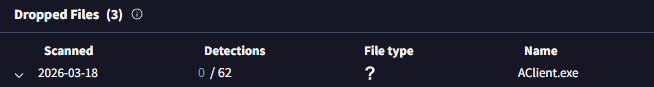
still in the relations tab, we can see the dropped file
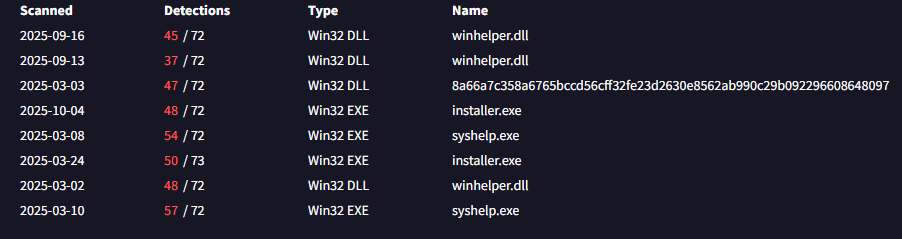
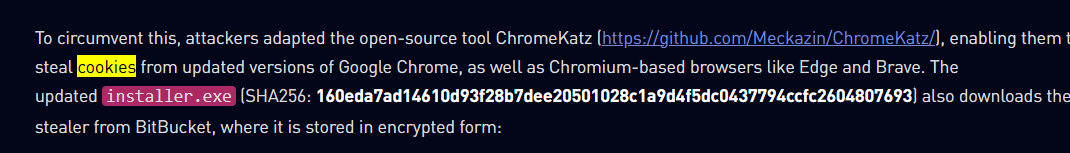
the second hash in question 3 comes from the installer.exe fa102d4e3cfbe85f5189da70a52c1d266925f3efd122091cdc8fe0fc39033942. searching this hash from VT gives us this information:
IP Analysis and Attribution
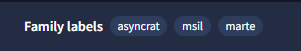
we know that the flag IP is 101.99.76.120. looking it up at Virus total report for the relations tab we will see this:
and one name keeps popping up in the family labels
checking the community notes, we found an article about asyncrat.
searching for the word "Cookies" in the article we found the tool the attackers used to steal cookies.
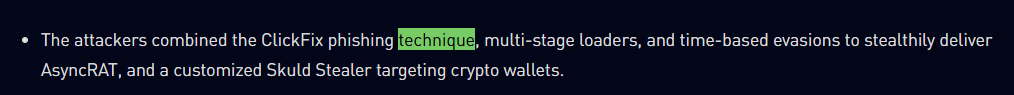
searching for the word technique, we found the main phishing technique the attackers used as well as more details about their attack.
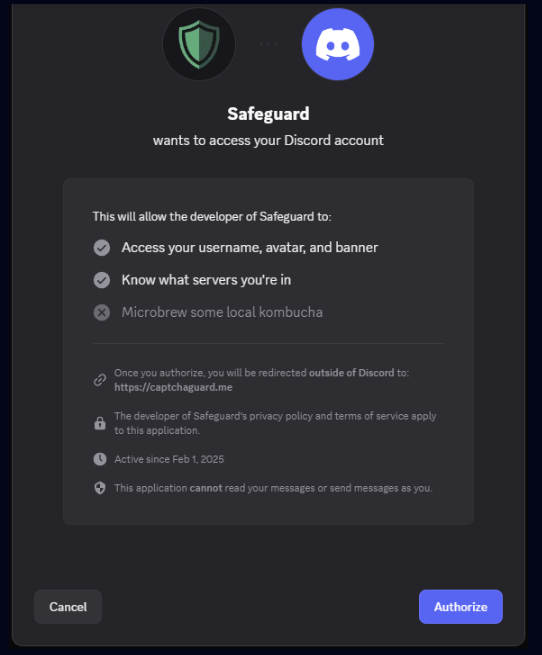
according to the report, the attackers used discord, most especially their authorization bot captchaguard.
- →the Relations tab in VirusTotal is where you start. execution chain, dropped files, related hashes, it's all right there
- →one hash leads to another through shared infrastructure. following that thread is how you get the full picture of how the deployment actually worked
- →ClickFix sidesteps attachment scanning by making the victim run the payload themselves. no attachment, nothing to flag
- →community notes on VirusTotal are worth reading. other analysts leave context there that ties IOCs back to actual threat reports